Cybersecurity and Access Control: Critical Risks in SCADA and Energy Systems
Introduction
With digitalization, energy facilities are no longer composed solely of physical equipment. While SCADA systems, remote access infrastructures, cloud integrations, and data analytics platforms improve operational efficiency, they also expand the attack surface. Industrial Control Systems (ICS), traditionally designed as isolated environments, are now integrated with corporate networks and even the internet [2][3]. This transformation has made energy generation and distribution infrastructures more visible and more vulnerable to cyber threats.
A security breach targeting SCADA systems does not merely result in data loss; it may cause operational disruption, physical damage, and even risks to human safety [1][2]. For this reason, cybersecurity in the energy sector is no longer just an IT responsibility—it is a fundamental component of operational continuity.
This article examines the most critical security risks in energy and SCADA environments from the perspectives of attack surface expansion, Identity and Access Management (IAM), network segmentation, and security monitoring. It also evaluates how these risks materialize in energy facilities and how an integrated security approach can be designed.
TL;DR
- SCADA and ICS systems are no longer isolated; integration with IT networks and the internet has expanded the attack surface [2][3].
- A cyber breach in energy facilities may lead not only to data loss but also to operational disruption and physical risk [1][2].
- Identity and Access Management (IAM) is a critical defense layer against vulnerabilities such as privilege escalation and default credentials [4][5].
- Network segmentation and the Purdue Model are foundational architectural principles for protecting OT networks [3][5].
- Without logging, monitoring, and anomaly detection mechanisms, security cannot be sustained [4][5].
- Concepts and the Expanding Attack Surface
Industrial Control Systems (ICS) is a general term for systems that monitor and control physical processes. This includes components such as Supervisory Control and Data Acquisition (SCADA) systems, Distributed Control Systems (DCS), and Programmable Logic Controllers (PLC) [2][4]. Energy generation facilities, transmission and distribution infrastructures, water treatment plants, and heavy industry are directly dependent on these systems.
- IT–OT Convergence and the Air-Gap Myth
Traditionally, ICS environments were designed using an “air-gap” approach—physically isolated architectures separated from the internet. However, due to operational efficiency needs, remote access requirements, and data analytics demands, this isolation model has largely disappeared [2][3].
Integration of ICS systems with corporate IT networks and even cloud infrastructures has significantly expanded the attack surface [2]. This transformation has introduced new attack vectors in energy facilities. Weak boundary protection and poorly defined security policies are now among the most frequently exploited vulnerabilities [3].
- What Is the Attack Surface?
The attack surface refers to the total set of potential entry points through which an attacker can gain access to a system. In SCADA and ICS environments, this may include:
- Remote access services (VPN, RDP, etc.)
- Web-based SCADA interfaces
- Open ports on PLC and RTU devices
- Outdated firmware and software
- Default usernames and passwords
A breach in SCADA systems is not limited to data manipulation. In energy production systems, it may lead to operational disruption, physical equipment damage, and safety risks [1][2]. Unlike traditional IT security incidents, ICS security breaches can directly impact the physical world.
- Identity and Access Management (IAM) Risks
A significant portion of security incidents in SCADA and ICS environments do not result from sophisticated zero-day exploits but from weak access control practices. Default credentials, shared user accounts, and lack of role separation create direct entry points for attackers [4][5].
- Default Credentials and Shared Accounts
Many industrial devices are delivered with default usernames and passwords. Failure to change these credentials is one of the most common vulnerabilities in ICS environments [4].
Shared accounts used on PLC and RTU devices create authentication and accountability issues.
In energy facilities, when maintenance teams, system integrators, and third-party vendors access systems through the same account, it becomes difficult to trace who performed specific actions. This complicates incident response and forensic investigations.
- Privilege Escalation Risk
Role-Based Access Control (RBAC) is widely used in industrial environments. However, poorly defined roles or overly permissive configurations increase the risk of privilege escalation [4].
For example:
- An operator having configuration modification privileges
- Maintenance personnel being able to change production parameters
- A remote access account having administrative rights
Such misconfigurations facilitate both horizontal and vertical movement within the system for attackers.
- Remote Access and VPN Risks
Remote access is necessary for operational continuity in energy facilities. However, access provided via VPN, RDP, or web interfaces constitutes one of the most critical components of the attack surface [1][3].
Following the integration of ICS systems with corporate networks, deficiencies in boundary protection and weak authentication mechanisms can lead to serious security vulnerabilities [3].
In environments where Multi-Factor Authentication (MFA) is not implemented, a compromised user password may provide access to the entire control layer.
The IAM layer represents the first line of defense in SCADA security. However, access control alone is not sufficient. If identity-based security measures are not supported by network architecture, it becomes difficult to prevent an attacker from moving laterally within the system.
- Network Segmentation and the Purdue Model
Identity and Access Management (IAM) provides user-based security. However, in ICS environments, authentication alone is not enough. If an attacker compromises an account and can move freely within the network (lateral movement), system integrity is placed at serious risk.
For this reason, network segmentation and layered architectural approaches are fundamental building blocks of ICS security [3][5].
- Defense-in-Depth Approach
In SCADA and ICS security, the “defense-in-depth” approach is widely adopted. This approach means implementing multiple layers of defense rather than relying on a single security mechanism [1][5].
In energy facilities, these layers typically include:
- Physical security
- Network segmentation
- Firewalls and DMZ
- Access control (IAM)
- Monitoring and logging systems
If one layer is compromised, the remaining layers are expected to contain or limit the attack.
- The Purdue Model and Layered Architectures
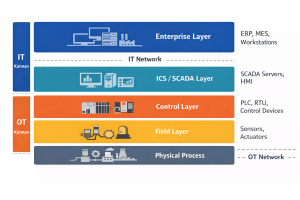
(Figure 1. The Purdue model illustrates the reference architecture that limits the attack surface by separating the IT and OT layers.)
The Purdue Enterprise Reference Architecture (PERA) model recommends designing industrial networks in layered structures. In this model:
- Level 0–1: Physical process and sensors
- Level 2: Control systems (PLC, HMI)
- Level 3: Operations management
- Level 4–5: Enterprise IT systems
Logical separation of IT and OT networks prevents attacks from directly propagating from upper layers to lower control layers [5]. In ICS environments, weak boundary protection and misconfigured network transitions are among the most frequently exploited vulnerabilities [3].
- What Happens Without Segmentation?
In an energy facility without proper segmentation, the following scenario is possible:
- Compromise of the corporate email system
- Access to a SCADA server located within the same network segment
- Manipulation of PLC communication protocols
- Operational disruption
Without segmentation, a breach in the IT environment can rapidly escalate into the OT environment, increasing the likelihood of physical impact and production interruption.
Uncontrolled integration of ICS systems with IT networks expands the attack surface and shortens the attack chain [2][3].
Network segmentation reduces the attacker’s speed of movement and limits the blast radius of a security incident. However, for segmentation to be effective, network traffic must be monitored and anomalies must be detected.
- Logging and Security Monitoring (Monitoring & Detection)
In ICS and SCADA environments, security cannot be ensured solely by restricting access or segmenting networks. Sustainable security requires continuous visibility into what is happening within the system. Logging and security monitoring mechanisms play a critical role in early detection of attacks and limiting their impact [4][5].
- Why Is Logging Critical?
In industrial environments, many security breaches remain undetected for weeks or even months. One of the primary reasons is the lack of sufficient log collection and centralized monitoring systems in OT networks [3][4].
In energy facilities, the following events should be logged:
- Failed and successful login attempts
- Privilege changes
- Configuration updates
- PLC program modifications
- Remote access connections
Without these records, incident response and root cause analysis become nearly impossible.
- IDS, Anomaly Detection, and Machine Learning
In ICS security, traditional signature-based Intrusion Detection Systems (IDS) may not be sufficient on their own, since many attacks are carried out using legitimate protocols. Therefore, network traffic analysis and anomaly detection approaches have gained importance [4].
Machine learning-based systems can:
- Model normal operational behavior
- Detect abnormal PLC commands
- Identify unusual traffic volume patterns
However, these systems do not replace fundamental security controls; they function as complementary defense layers [4][5].
- What Is Lost Without Logging?
Consider a hypothetical scenario in an energy facility:
- A remote access account is compromised.
- The attacker makes subtle changes to PLC parameters.
- Production efficiency decreases, but no physical failure occurs.
Without proper logging and monitoring, this situation may be misinterpreted as a mechanical issue or operational fluctuation rather than a security breach.
As a result:
- The attack may remain undetected for an extended period
- Financial losses may accumulate gradually
- Forensic investigation becomes extremely difficult
- Trust in operational data is compromised
In ICS environments, visibility is as important as protection. Without logs, organizations not only lose evidence—but also lose control.
If a centralized logging and alerting system is not in place, such changes may go undetected for an extended period. As a result, operational losses may increase, and the root cause of the incident may remain unidentified.
Logging and monitoring mechanisms may not completely prevent an attack; however, they limit its impact and reduce response time. In energy facilities, response time is directly correlated with operational loss.
- Energy Facility Scenario: What Happens Without Layered Security?
Consider a hydroelectric power plant (HPP) environment.
The facility:
- Is monitored via SCADA
- Allows maintenance teams to access systems remotely through VPN
- Shares data with the corporate network
Step 1 — Weak IAM
A maintenance account used for remote access is protected only by a username and password. Multi-Factor Authentication (MFA) is not implemented. The account also has broad privileges.
The password is compromised through a phishing attack.
Such weak access control practices are among the most common vulnerabilities in ICS environments [4][5].
Step 2 — Lack of Segmentation
There is insufficient segmentation between the corporate IT network and the OT network. The VPN connection provides direct access to the SCADA server.
The attacker:
- Connects to the SCADA server.
- Observes PLC communication traffic.
- Makes minor modifications to operational parameters.
Weak boundary protection and misconfigured network transitions are common exploitation points in ICS environments [3].
Step 3 — Insufficient Logging and Monitoring
There is no centralized log collection or real-time alerting mechanism in place. The parameter changes are not detected immediately.
Outcome:
- Turbine efficiency decreases
- Energy production capacity drops
- Operational costs increase
- The root cause of the incident cannot be identified
A breach in SCADA systems does not only impact data security; it poses risks to operational continuity and physical safety [1][2].
- What If a Layered Security Approach Had Been Implemented?
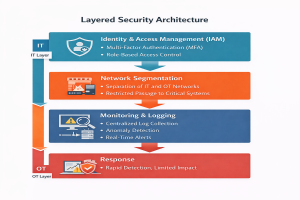
(Figure 2. Illustrates the layered security architecture and fundamental defense steps applied from the IT down to the OT layer.)
If, in the same facility:
- MFA had been implemented,
- IT and OT networks had been segmented,
- Permissions had been defined on a role-based and least-privilege basis,
- Real-time log analysis had been in place,
the attacker’s progression could have been detected at an early stage and the impact area could have been contained.
This scenario demonstrates why IAM, segmentation, and monitoring layers must operate together in ICS security.
- Renewasoft Security Approach: Integrated and Layered Architecture
Cybersecurity in energy facilities cannot be achieved through a single product or a single security control. SCADA and OT environments require an integrated approach that combines access control, network architecture, monitoring systems, and operational processes.
The Renewasoft approach treats security not as a separate layer, but as a natural component of the operational architecture.
- Structured Approach to Identity and Access Control
In energy facilities, core IAM principles should be embedded into system architecture, including:
- Role-based authorization
- Privileged account management
- Remote access control
- Monitoring of critical transaction logs
This approach provides not only user authentication but also authorization boundaries and traceability. As a result, privilege escalation risks are minimized [4][5].
- Segmentation and Operational Separation
In the Renewasoft architecture:
- IT and OT layers are logically separated
- SCADA data flows through controlled transition points
- Direct external access to critical control layers is prevented
This structure aligns with the defense-in-depth principle and reduces the attack surface [1][5].
- Logging, Monitoring, and Operational Visibility
In energy facilities, security is not only about prevention — it is about visibility.
Through centralized log collection, alert generation, and operational data analytics:
- Privilege changes can be tracked
- Suspicious connections can be detected
- Abnormal behaviors can be identified at an early stage
This approach enables the combined evaluation of security and operational performance data.
- Where Security and Operations Converge
SCADA security is not purely an IT matter. It is directly related to turbine efficiency, energy production capacity, and maintenance planning.
A secure architecture:
- Reduces the risk of unplanned downtime
- Minimizes the likelihood of unauthorized intervention
- Enhances the reliability of operational decision-support systems
For this reason, cybersecurity in energy facilities is a component of operational continuity — not a standalone project.
- Conclusion and Evaluation
Cybersecurity in energy facilities is no longer solely an information security issue; it is directly linked to operational continuity, physical safety, and economic sustainability. As SCADA and ICS systems integrate with IT networks and the internet, the attack surface inevitably expands [2][3]. When combined with access control weaknesses, poor segmentation, and inadequate monitoring, this expansion creates critical risks.
Identity and Access Management (IAM) controls the initial point of contact. Network segmentation limits the spread of attacks. Logging and security monitoring enable early detection. In environments where these layers are not jointly implemented, a security breach can result in operational disruption and physical damage risk [1][5].
Security in energy facilities cannot be reduced to a single product or control mechanism. A layered and integrated architecture is necessary not only to prevent attacks, but also to limit impact and reduce response time.
As a next step, it is recommended that existing SCADA and OT architectures be evaluated under three main headings:
- Access control and privileged account management
- IT–OT segmentation level
- Logging and incident response capability
This evaluation represents not merely a technical checklist, but the development of an operational risk map.
- Frequently Asked Questions
1- Why can’t SCADA systems be protected solely with traditional IT security?
ICS and SCADA systems control physical processes. Security breaches can therefore lead directly to operational disruptions and physical consequences [1][2]. In addition, many ICS protocols were designed with performance and availability in mind — not security. Therefore, traditional IT security alone is insufficient.
2- Is air-gap still a valid security approach?
In modern energy facilities, full isolation is practically unrealistic. Due to remote access needs, data analytics, and integration requirements, ICS systems are connected to corporate networks [2][3]. Segmentation and access control have effectively replaced pure air-gap strategies.
3- Which is the most critical security layer: IAM, segmentation, or monitoring?
If one of these layers is missing, risk increases. IAM controls identity verification. Segmentation limits the spread of an attack. Monitoring enables detection of breaches [3][5]. Security is achieved only when these layers function together.
4- Are these measures necessary for small-scale energy facilities?
Yes. Cyberattacks do not discriminate by scale. Even small facilities face significant risks from remote access exposure, default credentials, and weak segmentation [4][5].
5- Is machine learning alone sufficient for ICS security?
No. Machine learning-based anomaly detection is beneficial, but it does not replace fundamental access control, segmentation, and logging mechanisms [4][5]. Defense must be layered.