OT/IT Network Segmentation and Micro-Segmentation
Secure SCADA Architecture for HPPs: Purdue Model, IEC 62443 and Zero Trust
Renewasoft | 2026
Level: Advanced Audience: SCADA Engineer, HPP Operator, CTO, Infrastructure Investor
Introduction: The Security Prerequisite for Digital Transformation
Efficiency targets in HPP operations are rapidly making real-time monitoring, remote access, centralized reporting and AI-based predictive analytics standard practice. Hydrowise, positioned as a platform that collects real-time data from SCADA and IoT sensors to monitor plant performance and produce production/water flow forecasts and early warning/predictive maintenance outputs, is a practical example of this transformation[13].
However, this digitalization amplifies the same question at most sites: How do we protect control layers while securely exporting data? NIST SP 800-82r3 emphasizes that security measures must be carefully designed due to the performance, reliability and safety requirements of OT systems[1].
At this point, OT/IT network segmentation and micro-segmentation become not merely a compliance item, but an architectural prerequisite for secure digital energy management in HPPs. Segmentation limits the attacker’s ability to pivot from IT to OT, narrows critical control paths with least privilege, and defines data flow to platforms like Hydrowise through a controlled conduit[1][2].
► https://renewasoft.com.tr/index.php/tr/hizmetimiz/
TL;DR — Executive Summary
- OT/IT separation is an architectural reality where IT security practices cannot be directly copied to OT due to latency, determinism and safety requirements[1].
- Flat networks facilitate lateral movement from IT to OT; dual-homed systems, weak authentication and open remote access channels become pivot points[5][6].
- The Purdue model + DMZ approach establishes a mandatory enforcement boundary between OT and the corporate network, making data flows auditable[1].
- Micro-segmentation in Zero Trust architecture implements the never trust, always verify principle through Policy Enforcement Points (PEP) in practice[2].
- The path to secure Hydrowise integration is isolating the OT data collection layer with DMZ/jump server/micro-segmentation and opening only allowed (allowlist) data flows[13].
Paradigm Shift: IT/OT Separation Through the Purdue Model
OT systems (SCADA, DCS, PLC-based topologies) monitor and control physical processes; therefore, security design must address safety and continuity objectives alongside the CIA triad. NIST SP 800-82r3 defines adapting security measures to OT’s unique performance, reliability and safety requirements as its foundational framework[1].
| Criterion | IT Network | OT Network |
|---|---|---|
| Traffic Pattern | Variable, user-driven | Deterministic, repeatable, predictable |
| Latency Tolerance | Seconds to minutes acceptable | ms-level jitter affects process stability |
| Lifecycle | 3-5 years, regular updates | 15-25 years, legacy devices prevalent |
| Priority Order | Confidentiality → Integrity → Availability | Availability → Safety → Integrity |
| Anomaly Detection | Difficult: high variance | Opportunity: deterministic baselining |
Table 1: IT vs OT Network Characteristics Comparison [1]
The challenging aspect of this transformation is that data in HPPs no longer stays solely in the control room. Platforms like Hydrowise increase the need for OT-to-IT/Cloud data flow[13]. The modern threat landscape has demonstrated that the OT/IT boundary cannot be managed with a single firewall. In the 2015 Ukraine attack, adversaries exploited VPN paths from the corporate network to OT; the absence of 2FA amplified risk and breaker operations were executed via HMIs[5].
 Infographic: Purdue Model + IEC 62443 Security Zones and Communication Conduits [1][9]
Infographic: Purdue Model + IEC 62443 Security Zones and Communication Conduits [1][9]
IEC 62443: Security Zones and Communication Conduits
The most valuable practical contribution of the IEC 62443 approach is thinking of the network not as subnets but as security zones and the communication conduits connecting them. ENISA addresses the zoning/conduit approach within the framework of deriving security levels based on threat actor profiles[9]. Designing a conduit means pre-defining which ports/protocols/commands will pass between two zones.
| Zone | Scope | Critical Assets | Conduit Constraint |
|---|---|---|---|
| Zone A: Safety | Protection relays, interlocks | SIS, emergency stop, trip | Read-only telemetry output only |
| Zone B: Control | PLC/RTU, field switches | Governor PLC, gate PLC | Only authorized HMI→PLC commands |
| Zone C: Supervisory | SCADA, historian, HMI | SCADA server, collector | DPI + ML baseline monitoring |
| Zone D: OT DMZ | Jump server, log broker | Bastion, data diode, syslog | MFA + time-based + session recording |
| Zone E: Enterprise | ERP, SOC/SIEM, Cloud | Corporate AD, Hydrowise UI | No direct OT access |
Table 2: IEC 62443 Security Zones — HPP Reference Architecture [1][9]
Attack Surface Mapping: HPP Vulnerabilities
To properly design network segmentation, one must first translate the question ‘where can attacks originate?’ into an HPP-specific attack surface map. NIST defines OT topologies and components within this framework and lists typical vulnerability classes[1].
⚠ Technical Note: Vulnerable Areas in HPPs
Remote Access (VPN/RDP): The Ukraine attack report highlights that adversaries discovered and exploited VPN connections; absence of 2FA created risk and recommends remote access DMZ/jump host/split tunneling shutdown as countermeasures[5].
Dual-homed Systems: The ICS tactics framework explains that adversaries use default passwords and dual-homed devices for lateral movement. In flat networks, there is no segment barrier[6].
Engineering Workstations: PLC/RTU programs, governor setpoints are typically managed from EWS. High-priority attack surface as they are close to OT and require USB/vendor software[1].
Legacy Protocols: Some OT protocols were not born with security design. NIST notes that OT firewalls can perform DPI with DNP3/CIP/Modbus parsers[10].
Bowman Dam Breach (2013): Unauthorized access to the Bowman Dam SCADA in the US; water level, temperature and sluice gate status data was compromised. Remediation cost: $30,000+[12].
Defense Layers and Zero Trust
Layered Defense: VLAN / Firewall / DMZ / Jump Server / Data Diode
| Layer | Technical Function | HPP Implementation |
|---|---|---|
| DMZ | Blocks direct access from corporate network to OT; centralizes services at a single point [1] | Hydrowise OT gateway, log broker, time sync proxy located in DMZ |
| Jump Server | Routes OT access through a single controlled hop point [5] | MFA + time-based + session recording; split tunneling disabled |
| Firewall (DPI) | deny-all / permit-by-exception; stateful + DPI [10] | OT NGFW: Modbus FC, DNP3, OPC UA parser for command-level filtering |
| Data Diode | OT→DMZ unidirectional data flow; physically eliminates C2 channel [1] | All reverse flow physically blocked except critical telemetry |
| VLAN | Valuable for initial segmentation; trunk/routing/ACL bypass risk [10] | Should be supported with physical separation + enforcement devices where possible |
Table 3: Layered Defense Components [1][5][10]
Zero Trust and Micro-Segmentation
Zero Trust makes access decisions with least privilege on every request under the assumption that the network may already be compromised. NIST SP 800-207 explains that in micro-segmentation, resources are placed in separate segments and each segment is protected by a gateway/PEP[2]. In OT, this means cell/area-based segments, engineering workstation→PLC program download flows open only during defined maintenance windows, and HMI→PLC commands arriving only through operator role + MFA + designated jump host.
Deterministic Traffic Baselining
Traffic patterns in OT networks are far more deterministic than IT. NIST emphasizes that this determinism is critical for anomaly detection with IDS/IPS/BAD/SIEM and recommends tuning sensors in learning mode according to OT traffic[1][10].
Protocol Security: OPC UA and IEC 62351
The OPC UA security model includes client/server authentication, X.509 certificates, communication integrity/confidentiality and audit trail support[13]. IEC 62351 focuses on communication security for energy control protocols such as IEC 60870-5 and IEC 61850[14].
Technical Risk Scoring Model
NIST defines risk as a function of impact and likelihood[3]. NREL’s VaR framework formulates how risk can be reduced through control implementation level (CI)[7]:
L = Event likelihood (0-1) | CI_seg = Segmentation maturity (0-1) | I = Impact (0-1)
| Status | L | CI_seg | I | VaR |
|---|---|---|---|---|
| Baseline (VLAN exists, limited DMZ) | 0.40 | 0.20 | 0.70 | 0.224 |
| Target (DMZ+jump+micro-seg+DPI) | 0.40 | 0.70 | 0.70 | 0.084 |
Table 4: NREL VaR — Impact of Segmentation Maturity on Risk Indicator [7]
Segmentation/micro-segmentation maturity reduces the risk indicator by ~62% (0.224 → 0.084). This is not a definitive result; it is a decision-support metric for prioritizing investment[7][3].
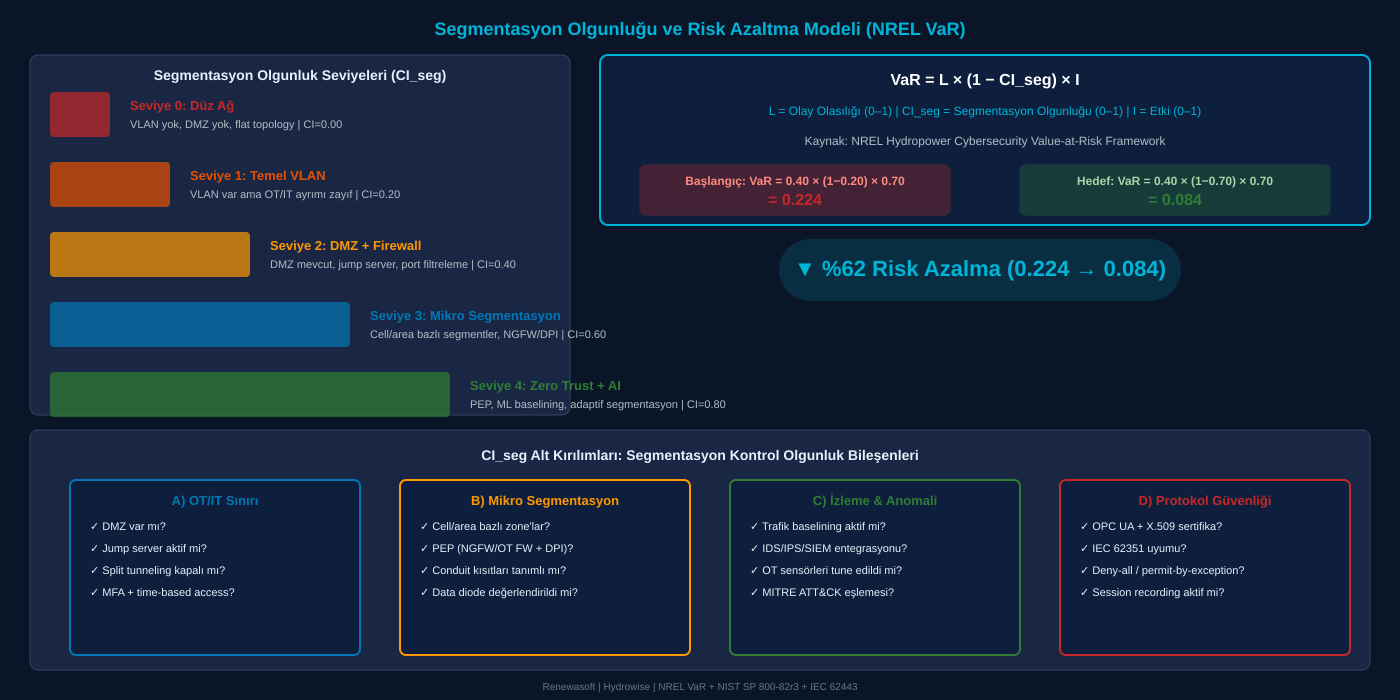 Infographic: Segmentation Maturity Levels and NREL VaR Risk Reduction Model [7]
Infographic: Segmentation Maturity Levels and NREL VaR Risk Reduction Model [7]
Case Study: HPP Attack Simulation
💥 Evidence-Based Background
Ukraine 2015: Adversaries executed operations not only through malware but by directly using control systems; BlackEnergy/KillDisk facilitated access and delayed recovery[5].
ICS-CERT: KillDisk corrupted MBR rendering systems unusable; Windows-based HMIs and serial-to-Ethernet firmware were affected[6].
Bowman Dam 2013: Unauthorized SCADA access; $30K+ remediation cost[12].
| # | Phase | Technical Step | Segmentation Impact |
|---|---|---|---|
| 1 | Initial Access | Spearphishing to enter corporate network [5] | IT segmentation forms the first barrier |
| 2 | Credential Access | Domain credentials + VPN path discovery [5] | MFA + PAM blocks credential harvesting |
| 3 | Pivot (IT→OT) | Lateral movement to OT via dual-homed EWS [6] | DMZ + jump server + data diode prevents pivot |
| 4 | Lateral Movement | Spreading within OT via RDP/SMB [6] | Micro-segmentation provides cell-based isolation |
| 5 | Impact | Breaker/gate control, wiper, DoV/DoC [5][6] | Segmentation hardens steps 3-4, limiting impact |
Table 5: Attack Simulation Flow and Segmentation Impact [5][6]
DOE’s document emphasizes that an HPP cyber incident can affect public safety, critical infrastructure and grid energy distribution[8]. In a 100 MW HPP, a 4-hour forced outage = 400 MWh loss + market/imbalance and restart costs.
Hydrowise: Secure Integration Architecture
Hydrowise is an end-to-end digital energy management platform that collects real-time data from SCADA/IoT to deliver production forecasting, predictive maintenance, water flow prediction and EPIİAŞ market integration[13]. The security architecture must simultaneously: (1) preserve OT control integrity, (2) securely transport data to the analytics layer.
DMZ Reference Architecture
| Zone | Components | Security Controls |
|---|---|---|
| Zone 0-2 (Field/Control) | PLC/RTU, I/O networks, turbine-gate control cells | Micro-seg: each cell isolated; DPI for Modbus FC control |
| Zone 3 (Supervisory) | SCADA servers, historian, HMI | HMI→PLC only from authorized hosts/protocols; ML baseline |
| Zone 3.5 (OT DMZ) | Hydrowise OT gateway, jump server, log broker | MFA + time-based + session recording; optional data diode |
| Zone 4-5 (Enterprise/Cloud) | SOC/SIEM, corporate IAM, Hydrowise UI | No direct OT access; controlled flow through DMZ |
Table 6: Hydrowise-Integrated HPP OT/IT DMZ Reference Architecture [1][2][9]
Critical design principle: The Hydrowise OT collector only collects read-only telemetry; it does not generate control commands. Identity verification is X.509 certificate-based via the OPC UA security model[13].
🔍 HPP-Specific AI Capabilities
Water Flow Prediction: ML model trained on meteorological data (rainfall, snowmelt, temperature), watershed parameters and historical flow records. 72-hour forecast window.
Production Forecasting: Integrated forecast combining reservoir level + water flow + turbine efficiency curves + market price signals. Output aligned with EPIİAŞ DAM/IDM periods.
Predictive Maintenance: Multi-variable anomaly scoring from turbine vibration, bearing temperature, oil quality, winding insulation resistance.
EPIİAŞ Integration: Optimization integrated with DAM/IDM price signals. Automated bidding, imbalance risk analysis and revenue maximization.
Frequently Asked Questions (FAQ)
Q1: Can VLAN alone provide OT/IT separation?
VLANs are valuable for cost efficiency; however, NIST recommends physical separation and enforcement devices (firewall/unidirectional gateway) where possible. VLANs can be bypassed through trunk/routing/ACL gaps[1][10].
Q2: Does micro-segmentation degrade OT latency?
If poorly designed, yes. When selecting PEPs (NGFW/OT firewall), throughput/latency tests must be conducted; sensors should be tuned in learning mode; allowlists for critical control flows must be clearly defined[1][2].
Q3: What belongs in the DMZ?
Data collectors, jump host, log broker, time sync proxy. Direct domain controller dependency to OT makes OT dependent on IT reliability[1].
Q4: Is DPI necessary for OT firewalls?
Port-based filtering is the baseline; command/function differentiation in OT protocols is critical. NIST recommends DPI-capable firewalls as compensating controls for legacy devices[10].
Q5: Should Zero Trust be implemented gradually in OT?
Yes. First isolate critical assets with micro-segments and control access through jump hosts; then mature the policy engines[2].
Q6: How is remote access secured with Hydrowise?
Through a jump server in the DMZ, constrained by MFA and time-based access. Split tunneling disabled. OT collector/gateway in DMZ, only allowed data flows to Cloud[5][13].
Q7: How is segmentation’s contribution measured?
NREL VaR framework: VaR = L×(1-CI)×I. Segmentation maturity is scored within CI_seg; as DMZ, jump host, DPI, baselining controls increase, the risk metric decreases[3][7].
Conclusion and Next Steps
OT/IT segmentation and micro-segmentation are not just cybersecurity concerns in HPPs; they are integral to production continuity and safety objectives[1][10]. Hydrowise, when designed with proper segmentation, places digital energy management on a secure architectural foundation[13].