ICS Ransomware and APT Threats
Attack Lifecycle, Lateral Movement, and AI-Powered Defense
Hydrowise AI-Powered Hydroelectric Power Plant Management System
Renewasoft | 2026
Level: Advanced Audience: SCADA Engineer, HPP Operator, CTO, Infrastructure Investor
Introduction: Beyond Ransom — The Silent War in Industrial Control Systems
When the 2021 Colonial Pipeline attack triggered a 6-day fuel crisis across the eastern United States, the world experienced the tangible scale of ransomware threats to critical infrastructure[2]. Yet this incident was merely the tip of the iceberg. Behind the scenes, nation-state-backed Advanced Persistent Threats (APTs) were lurking deep within energy infrastructure for months — sometimes years — conducting reconnaissance, analyzing control logic, and waiting for the strategic moment[11].
Hydropower plants (HPPs) occupy a particularly critical position in this threat landscape. When an HPP’s SCADA system is compromised, the consequences extend far beyond data loss: uncontrolled gate operations, turbine overspeed events, dam safety violations, and cascading grid failures represent kinetic and environmental disasters. According to Dragos’ 2023 report, the energy sector remains the most targeted sector by ICS threat groups[3].
This article analyzes ransomware and APT threats targeting industrial control systems through the attack lifecycle (kill chain) lens[6], maps lateral movement mechanisms to HPP architecture-specific risks, and details how Renewasoft’s Hydrowise platform responds to these threats with AI-powered anomaly detection, adaptive segmentation, and end-to-end digital energy management[13].
Hydrowise is not merely a cybersecurity solution — it is an end-to-end digital energy management platform that collects real-time data from SCADA and IoT sensors to deliver production forecasts, predictive maintenance scenarios, water flow predictions, and EPIİAŞ market integration[13].
Concepts 101: Core Terminology
A baseline reference table for the technical terms used throughout this article:
| Term | Definition |
|---|---|
| ICS | Industrial Control System — hardware/software that monitors and controls physical processes (energy generation, water management). |
| APT | Advanced Persistent Threat — nation-state-backed, long-term, stealthy cyber attack campaigns. Goal: intelligence, sabotage. |
| Ransomware | Malware that encrypts data/systems and demands cryptocurrency ransom payment. |
| Kill Chain | Attack Lifecycle — model defining sequential stages of a cyber attack from reconnaissance to impact [6]. |
| Lateral Movement | Attacker’s horizontal progression from one system to another within the network (IT → DMZ → OT). |
| C2 (C&C) | Command and Control — attacker’s covert communication channel with compromised systems (HTTPS, DNS tunneling). |
| Dwell Time | Duration an attacker remains undetected in the network. APT median: 21 days [11]. |
| SIS | Safety Instrumented System — last line of defense ensuring process safety (TRITON target) [5]. |
Table 1: ICS Cybersecurity Core Terminology
TL;DR — Executive Summary
- ICS infrastructure faces a dual threat: nation-state APT campaigns pursue long-term sabotage while ransomware groups create operational disruption for immediate financial gain[3][11].
- The attack lifecycle (kill chain) is multi-stage: IT network penetration → lateral movement → OT discovery → ICS weapon deployment → kinetic impact. Average dwell time: 21 days for APT, 5 days for ransomware[6][11].
- Lateral movement is the most critical risk vector for HPPs: flat network topologies and DMZ absence facilitate attacker transition from IT to OT[4].
- Early detection is the key to business continuity: AI-based behavioral analysis can break APT stealth that remains invisible to traditional signature-based detection[13].
- Hydrowise as an end-to-end digital energy management platform combines DPI, ML anomaly detection, and adaptive segmentation with production forecasting, predictive maintenance, and EPIİAŞ integration to maximize both security and operational efficiency[13].
Paradigm Shift in the ICS and OT World
What Is ICS and Why Is It Different?
Industrial Control Systems (ICS) encompass all systems that monitor and control physical processes — from electricity generation to water management, petrochemicals to transportation. Comprising components such as SCADA, PLC, RTU, HMI, and DCS, these systems fundamentally differ from IT: the priority order is availability → integrity → confidentiality (the reverse of IT). A PLC’s 10ms control loop cannot tolerate latency; an HMI’s momentary loss of visibility means blind flight for the operator[8].
The Purdue Model (ISA-95/IEC 62443) defines this IT/OT separation through a five-layer reference architecture: Level 0 (physical process), Level 1 (PLC/RTU), Level 2 (HMI/SCADA), Level 3 (site operations), Level 3.5 (DMZ), and Levels 4-5 (enterprise IT/internet)[8]. The transitions between these layers are the critical nodes of the attack lifecycle.
APT and Ransomware: Two Distinct Threat Models
Understanding cyber threats targeting ICS infrastructure requires distinguishing two fundamental attack paradigms:
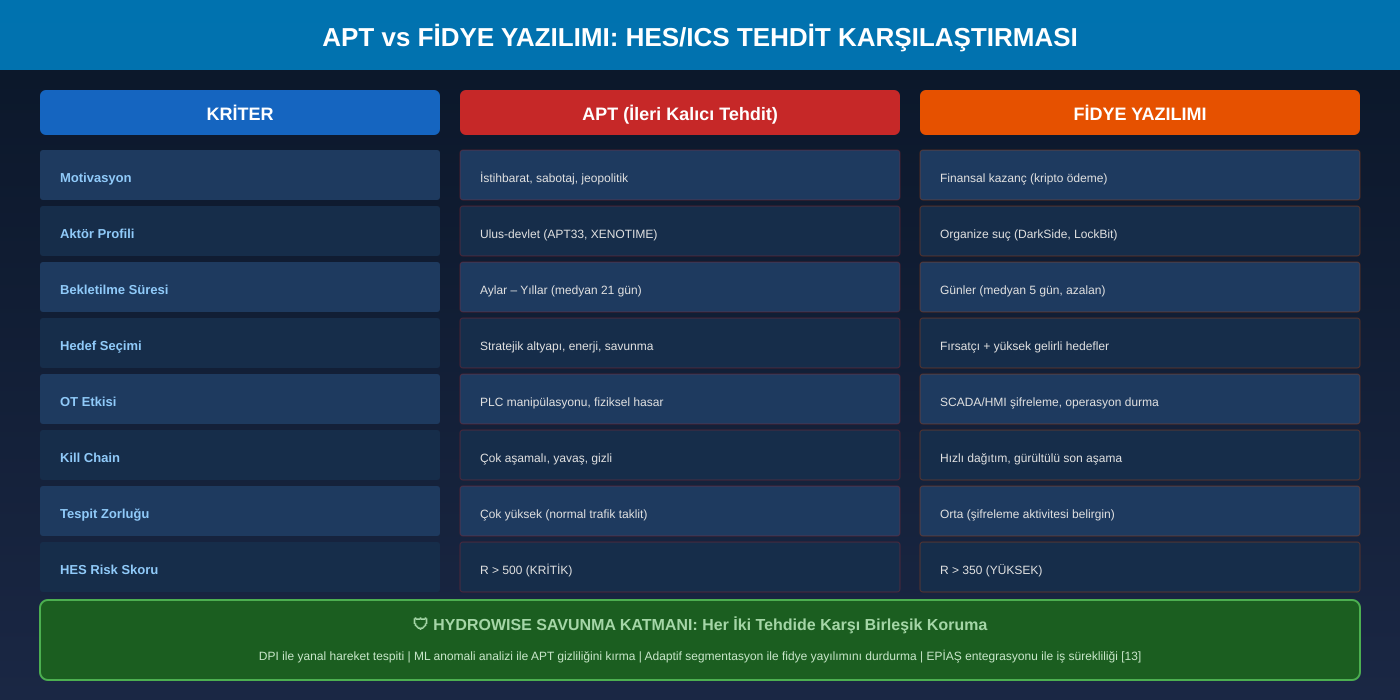
Infographic 1: APT and Ransomware Threat Comparison — HPP/ICS Perspective [3][5][11]
| Criterion | APT (Advanced Persistent Threat) | Ransomware |
|---|---|---|
| Motivation | Intelligence gathering, strategic sabotage, geopolitical advantage | Financial gain (cryptocurrency ransom payment) |
| Actor Profile | Nation-state backed: XENOTIME, ELECTRUM, CHERNOVITE [5] | Organized crime: DarkSide, LockBit, BlackCat [2] |
| Dwell Time | Median 21 days; months-years possible [11] | Median 5 days; rapidly declining trend [11] |
| HPP Impact | PLC logic manipulation → physical damage, SIS disabling [5] | SCADA/HMI encryption, historian DB loss → operational blindness [2] |
| Detection Difficulty | Very high — mimics normal traffic, low-and-slow [4] | Moderate — encryption activity is conspicuous but noticed late [4] |
Table 2: APT and Ransomware Threat Comparison [3][5][11]
🔍 Technical Note: Turning Points in ICS History
Stuxnet (2010): The first known ICS weapon. Malware infiltrated Iran’s Natanz facility via USB, altered the frequency converter control logic of Siemens S7-300 PLCs, and physically destroyed ~1,000 uranium enrichment centrifuges. Proved that PLC logic manipulation can cause kinetic damage[1].
Colonial Pipeline (2021): The DarkSide ransomware group infiltrated the IT network using a compromised VPN credential. IT system encryption led to precautionary OT operations shutdown — 6-day fuel crisis, $4.4M ransom payment. Concrete evidence of IT/OT dependency[2].
TRITON/TRISIS (2017): The XENOTIME threat group targeted a Middle Eastern petrochemical facility’s Safety Instrumented System (SIS — Schneider Triconex). Reprogrammed the SIS controller through the engineering workstation. Proved attackers’ intent to disable the last line of safety defense[5].
(Source: [1][2][5])
Attack Lifecycle: ICS Kill Chain
The SANS Institute’s ICS Cyber Kill Chain model[6] defines attacks targeting industrial control systems within a two-phase framework: (1) IT network penetration and establishment, (2) OT network transition and ICS weapon deployment. When combined with MITRE ATT&CK for ICS[4] technical classification, it becomes possible to concretely map both each stage of the attack and defense opportunities.
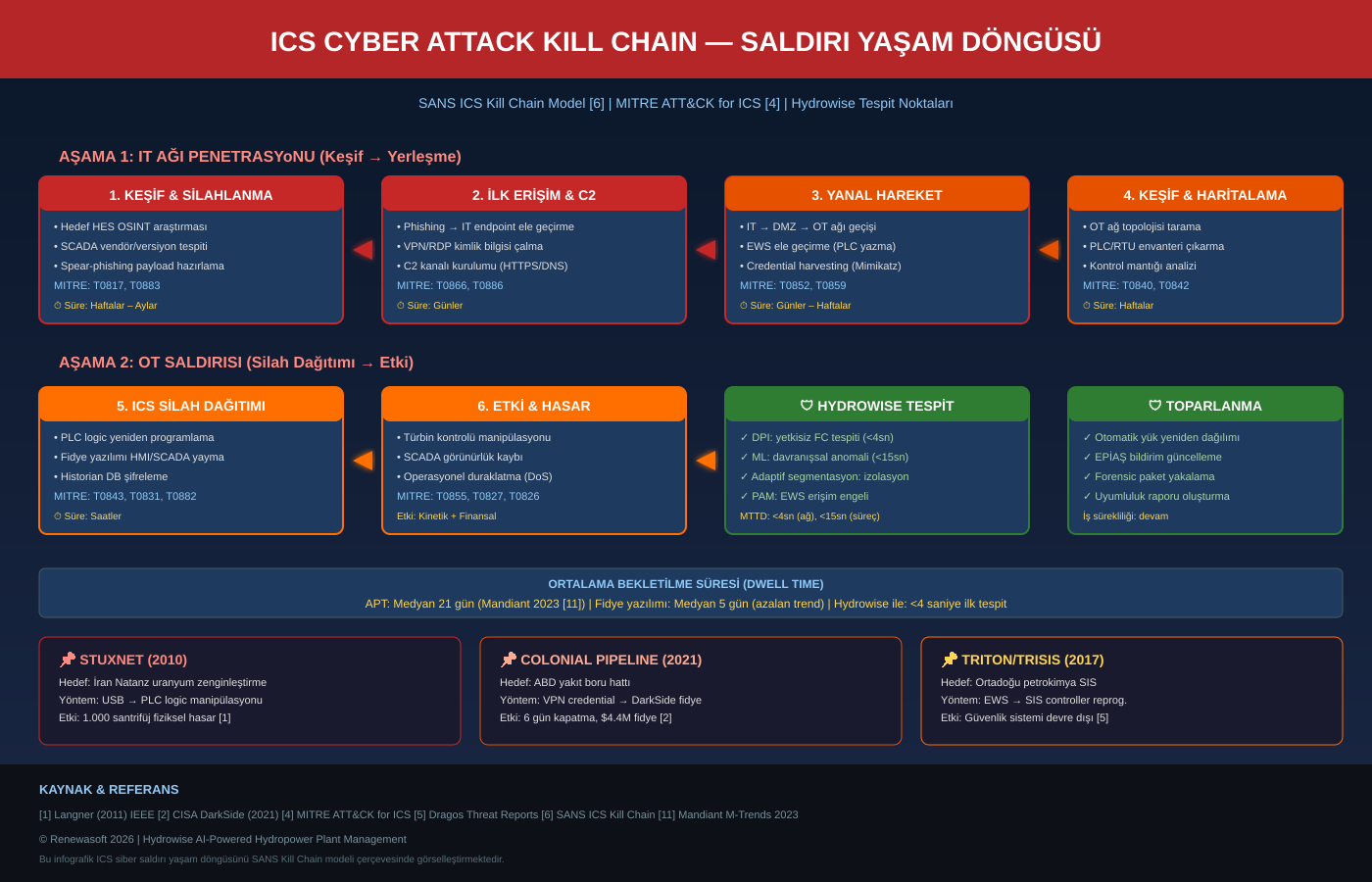
Infographic 2: ICS Cyber Attack Kill Chain — SANS Model [6] + MITRE ATT&CK for ICS [4] + Hydrowise Detection Points
| # | Stage | Technical Detail | MITRE ID | Duration |
|---|---|---|---|---|
| 1 | Reconnaissance & Weaponization | Target HPP OSINT research, SCADA vendor/version identification, spear-phishing payload preparation | T0817, T0883 | Weeks–Months |
| 2 | Initial Access & C2 | Phishing → IT endpoint, VPN/RDP credential theft, C2 channel establishment (HTTPS/DNS tunnel) | T0866, T0886 | Days |
| 3 | Lateral Movement | IT → DMZ → OT transition, EWS compromise, credential harvesting (Mimikatz, Pass-the-Hash) | T0852, T0859 | Days–Weeks |
| 4 | OT Discovery | OT network topology scanning, PLC/RTU inventory extraction, control logic analysis | T0840, T0842 | Weeks |
| 5 | ICS Weapon Deployment | PLC logic reprogramming, ransomware propagation to HMI/SCADA, historian DB encryption | T0843, T0831 | Hours |
| 6 | Impact & Damage | Turbine control manipulation, SCADA visibility loss, operational shutdown | T0855, T0826 | Immediate |
Table 3: ICS Kill Chain Stages — HPP Context [4][6]
Lateral Movement and Operational Posture Risk
Attack Surface Mapping: Weak Points in HPPs
The most critical and most defensible stage of the kill chain is lateral movement. Once an attacker gains initial access in the IT network, they must cross multiple network boundaries to reach the OT network — if those boundaries are properly implemented[7]. However, in many HPP installations these boundaries effectively do not exist:
⚠ Risk Box: 4 Critical Lateral Movement Paths in HPPs
1. Flat Network Topology: SCADA, engineering workstations, and corporate IT on a single Layer 2 broadcast domain. Attacker can see all traffic via ARP poisoning. Missing Purdue Level 3.5 DMZ is the most common root cause.
2. Dual-Homed Engineering Workstations (EWS): EWS connected to both corporate network and OT network serves as a natural bridge for attackers. RDP access, then direct control through PLC programming tools (TIA Portal, Studio 5000).
3. Shared Credentials: OT environments frequently use default passwords (admin/admin), shared service accounts, and non-rotated credentials. When one IT credential is stolen, OT access follows.
4. Remote Access VPNs: Post-COVID increase in remote maintenance demand has generally provided direct VPN access to OT network without MFA. This was the exact entry point for the Colonial Pipeline attack[2].
(Source: [2][4][7])
Business Continuity and Disaster Scenarios
Disaster scenarios that an attacker can create after successful lateral movement into the OT network:
| Scenario | Mechanism | HPP Impact |
|---|---|---|
| Ransom Encryption | HMI/SCADA/historian encryption → operator visibility loss | Switch to manual ops, production loss: ~$18K/hour [2] |
| PLC Manipulation | Governor PLC logic change → uncontrolled guide vane movement | Turbine overspeed → mechanical failure, $250K–$500K [1] |
| SIS Disabling | TRITON-style SIS controller reprogramming [5] | No last safety line → catastrophic potential |
| Data Wiping | Historian, SCADA config, PLC backup deletion | Recovery time extends to weeks, no forensic evidence |
Table 4: Disaster Scenarios When Attacker Reaches OT Network [1][2][5]
Defense Layers: Early Detection and Zero Trust
Breaking APT Stealth with Anomaly Analysis
APT attacks are designed to evade signature-based security tools — they do not use known malware signatures, prefer legitimate tools (living-off-the-land), and mimic normal traffic patterns. Traditional antivirus and firewall layers are therefore insufficient[4].
An effective defense strategy must be built on behavioral anomaly analysis: an ML model that learns the ‘normal’ behavior of every device, protocol, and process variable can detect deviations — however small. The NIST SP 800-207 Zero Trust architecture[7] provides the framework: ‘Never Trust, Always Verify.’
► NIST SP 800-207 Zero Trust Architecture → https://csrc.nist.gov/pubs/sp/800/207/final
► MITRE ATT&CK for ICS → https://attack.mitre.org/techniques/ics/
| Defense Layer | Effectiveness Against APT | Effectiveness Against Ransomware |
|---|---|---|
| DPI (Deep Packet Inspection) | Unauthorized Modbus FC, OPC UA session detection — captures covert recon traffic [13] | Pre-encryption file propagation traffic and SMB lateral movement detection [13] |
| ML Behavioral Analysis | Detects APT mimicking normal traffic through baseline deviation — most effective layer [13] | Abnormal file access patterns, mass encryption activity detection [13] |
| Micro-Segmentation | Stops lateral movement at IEC 62443 zone/conduit level [8] | Limits ransomware propagation to affected zone [8] |
| PAM (Privileged Access) | Eliminates direct RDP to EWS, MFA + session recording [13] | Blocks credential harvesting with MFA [13] |
Table 5: Defense Layer Effectiveness Against APT and Ransomware [7][8][13]
Technical Risk Scoring Model
To quantify HPP-specific risk from APT and ransomware threats, the FAIR methodology[9] has been adapted. Compliant with IEC 62443-3-2[8] and NERC CIP[10].
T = Threat Likelihood (1-10) | V = Vulnerability Exploitability (1-10) | I = Operational Impact (1-10)
Scenario Comparison: APT vs Ransomware
| Scenario | T | V | I | R | Rationale |
|---|---|---|---|---|---|
| APT: Governor PLC | 8 | 8 | 9 | 576 | Nation-state APT, Modbus TCP (no auth), turbine overspeed [2][6] |
| Ransom: SCADA/HMI | 7 | 7 | 7 | 343 | Organized crime, legacy OS/no EDR, operational blindness [2][11] |
| Ransom: Historian DB | 7 | 6 | 5 | 210 | Data loss, compliance violation, forensic loss [9] |
Table 8: APT and Ransomware Risk Scoring Comparison [9]
Hydrowise: End-to-End Digital Energy Management Platform
Platform Overview
Hydrowise is an AI-powered energy management platform designed to enable end-to-end digital transformation for hydropower plants. By collecting real-time data from SCADA and IoT sensors, the platform continuously monitors plant performance and provides reliable visibility across all critical operational parameters[13].
Cybersecurity is a critical component of this comprehensive platform. Rather than adapting enterprise IT security tools to OT — which introduce latency, generate false positives, and lack ICS protocol visibility — Hydrowise provides a purpose-built security layer that both breaks APT stealth and stops ransomware propagation[13].
Implementation Methodology
Before each implementation, Hydrowise analyzes the specific needs of the hydropower plant by training AI models with location-based meteorological data and historical production records. This analytical process identifies operational challenges, capacity limitations, water flow variability, and maintenance requirements[13]. As a result, Hydrowise precisely defines the issues to be addressed and establishes the most effective digital transformation strategy for the plant.
How It Works in 3 Steps
| # | Step | Description |
|---|---|---|
| 1 | AI-Powered Data Integration | Real-time operational data from SCADA, sensors, and IoT devices is securely collected and unified within the Hydrowise platform. Security events and process data are monitored from a single center. |
| 2 | AI-Powered Analysis | Operational parameters are processed using big data technologies. Network security events and process data are correlated for anomaly detection, production forecasting, and risk analysis. |
| 3 | Forecasting, Detection & Decision Support | ML algorithms: production forecasting, predictive maintenance, water flow prediction, anomaly detection (≤4s). EPIİAŞ market integration, automated reporting, and decision-support mechanisms deliver actionable intelligence [13]. |
Table 6: Hydrowise — How It Works in 3 Steps [13]
🔍 Technical Note: HPP-Specific AI Capabilities
Water Flow Prediction: ML model trained on meteorological data (rainfall, snowmelt, temperature), watershed hydrological parameters, and historical flow records. Hourly and daily resolution with a 72-hour forecast window.
Reservoir Level Monitoring: Real-time level sensor + flow prediction integration. Fill/drain curves and flood risk early warning for optimum water management.
Production Forecasting: Integrated forecast combining reservoir level + water flow + turbine efficiency curves + market price signals. Output aligned with EPIİAŞ DAM/IDM submission periods.
Predictive Maintenance: Multi-variable anomaly scoring from turbine vibration profile, bearing temperature trend, oil quality, winding insulation resistance. Maintenance window recommendation to prevent unplanned downtime.
EPIİAŞ Market Integration: Optimization integrated with Day-Ahead Market (DAM) and Intraday Market (IDM) price signals. Automated submission, imbalance risk analysis, and revenue maximization.
(Source: [13])
Case Analysis: Hybrid APT + Ransomware Attack Simulation on 200 MW HPP
The following scenario models an opportunistic ransomware attack following a nation-state APT campaign on a fictional 200 MW storage HPP (“Plant Alpha”) with four 50 MW Francis turbine-generator units. The plant uses Siemens S7-1500 PLCs, Modbus TCP, and OPC UA gateway[4].
| Day | Stage | Attacker Action | Hydrowise Detection |
|---|---|---|---|
| D1 | Initial Access | Spear-phishing → IT endpoint compromise. DarkSide variant deployment. | — (IT scope, Hydrowise is OT-focused) |
| D3 | Lateral Movement | RDP to EWS. Mimikatz credential dump. OT network scanning initiated. | 🟢 DPI: New Modbus scan traffic from EWS detected [13] |
| D7 | OT Discovery | PLC inventory extraction (S7comm read), control logic analysis, SCADA config dump. | 🟢 ML: Out-of-baseline S7comm session frequency anomaly [13] |
| D14 | Ransom Deployment | HMI/SCADA encryption initiated. Historian DB locked. Ransom note dropped. | 🔴 DPI: SMB mass file encryption traffic → auto-isolation [13] |
| D14+4s | Hydrowise Response | — | 🛡 Adaptive segmentation: affected zone isolated. Load transfer to healthy units. EPIİAŞ notification update [13]. |
Table 9: Hybrid APT + Ransomware Attack Timeline [4][13]
This scenario demonstrates a hybrid attack model where the APT reconnaissance phase facilitates ransomware deployment. Hydrowise’s DPI engine would have detected lateral movement traffic at D3, the ML model would have flagged out-of-baseline PLC communications at D7. When ransomware deployment began at D14, adaptive segmentation isolated the affected zone within seconds while the energy management layer automatically recalculated load distribution for remaining units and updated EPIİAŞ notifications[13].
Additionally, Hydrowise’s energy management layer provides critical value during post-attack recovery: automatically recalculates optimal load distribution across the remaining three units (3 × 50 MW), updates production capacity for EPIİAŞ market submissions, and the predictive maintenance module minimizes unplanned downtime[13]. Thus, the financial impact of a security event is mitigated not only through detection but through integrated energy management intelligence.
FAQ: Technical Deep Dive
Q1: What is the fundamental difference between APT and ransomware from an HPP security perspective?
APT campaigns are nation-state-backed, long-term, stealthy sabotage operations (median 21-day dwell time) targeting physical damage. Ransomware is financially motivated, fast, and noisy — creating operational disruption to demand ransom. HPPs require distinct defense layers against each[3][11].
Q2: How does Hydrowise detect APT traffic mimicking normal patterns?
The ML model learns ‘normal’ behavior for every device, protocol, and process variable through a 30-day baseline. Even though APT traffic appears legitimate, micro-level frequency, timing, and correlation deviations are detected[13].
Q3: At which kill chain stage is Hydrowise most effective?
Stage 3 (Lateral Movement) and Stage 5 (ICS Weapon Deployment). DPI catches lateral movement traffic, ML flags OT discovery activities, and adaptive segmentation stops ransomware propagation[4][13].
Q4: How does the plant continue operating if ransomware encrypts HMI/SCADA?
Hydrowise isolates the affected zone and automatically recalculates load distribution for healthy units. EPIİAŞ market notifications are updated. The predictive maintenance module optimizes the recovery process[13].
Q5: What impact would a Colonial Pipeline-style attack have on an HPP?
At Colonial, IT encryption caused precautionary OT shutdown. Same scenario at an HPP: SCADA visibility loss → manual operation → production loss (~$18K/hour) → EPIİAŞ imbalance penalty. Hydrowise’s IT/OT segmentation prevents this domino effect[2][13].
Q6: What is the defense against Stuxnet-style PLC logic manipulation?
Dual-layer detection: (1) Network — PLC programming sessions (S7comm writes) detected by DPI and correlated with change management records[4]. (2) Process — behavioral model detects downstream effects of PLC logic changes (turbine speed deviation, temperature trend)[13].
Q7: How do you minimize dwell time?
Hydrowise MTTD: network anomalies <4s, process anomalies <15s. Industry median: APT 21 days, ransomware 5 days. Continuous ML-based monitoring reduces dwell time to seconds. 30-day baseline + online learning adapts to seasonal changes[11][13].
Q8: Which compliance frameworks are supported?
IEC 62443[8], NIST CSF 2.0[12], NERC CIP[10], EU NIS2 Directive, ISO/IEC 27001 Annex A. Automated compliance reports — each control linked to Hydrowise telemetry and incident records[8][10][12][13].
Q9: How does EPIİAŞ market integration work during cyber incidents?
During an attack, Hydrowise automatically calculates remaining production capacity, updates DAM/IDM submissions, and performs imbalance risk analysis. The cybersecurity layer also protects market data channel integrity[13].
Q10: What is the deployment timeline?
Phased: Wk 1-2 (Site assessment + TAP deployment) → Wk 3-6 (Passive monitoring + baselining) → Wk 7-8 (Model validation + FP tuning) → Wk 9-10 (Active enforcement + training). Total: ~10 weeks, zero generation downtime[13].
Conclusion & Call to Action
Ransomware and APT threats targeting industrial control systems are no longer theoretical scenarios for HPP operators — they are realized and recurring attacks. Stuxnet proved physical destruction is possible, Colonial Pipeline demonstrated that IT/OT dependency can paralyze critical infrastructure, and TRITON showed attackers will target even the last line of safety.
Hydrowise responds to these threats as an end-to-end digital energy management platform: an integrated approach that stops lateral movement traffic with DPI, breaks APT stealth with ML behavioral analysis, limits ransomware propagation with adaptive segmentation, and combines all of this with production forecasting, predictive maintenance, and EPIİAŞ market integration[13]. Result: HPPs gain both cyber resilience and operational efficiency.