SCADA Security in Critical Infrastructure
Attack Surface Analysis and Defense Layers
Hydrowise AI-Powered Hydroelectric Power Plant Management System
Renewasoft | 2026
Level: Advanced Target Audience: SCADA Engineer, HPP Operator, CTO, Infrastructure Investor
Introduction: The Invisible Threat Behind the Turbine
Every 39 seconds, a cyberattack targets an internet-connected system somewhere in the world[1]. For most industries, a breach means data loss or financial damage. For a Hydroelectric Power Plant (HPP), a single compromised Programmable Logic Controller (PLC) can mean uncontrolled gate operations, turbine overspeed events, or cascading failures across an interconnected grid. The consequences are not abstract — they are kinetic, environmental, and potentially catastrophic.
Yet the operational technology (OT) environments that govern these assets were designed decades ago under a fundamentally different threat model: physical isolation. The Modbus RTU protocol, still the backbone of many HPP SCADA systems, was standardized in 1979[6]. It carries no authentication, no encryption, and no integrity checking.
That world no longer exists. The convergence of IT and OT networks has dissolved the air gap that once served as the primary defense. According to Dragos’s 2023 OT Cybersecurity Year in Review, threat groups targeting industrial control systems (ICS) increased by 35% year-over-year, with the energy sector remaining the most targeted vertical[2].
This post maps the attack surfaces unique to hydropower SCADA environments against established frameworks (Purdue Model[3], MITRE ATT&CK for ICS[4], IEC 62443[8]), and details how Renewasoft’s Hydrowise platform addresses each layer of risk through AI-driven anomaly detection, adaptive network segmentation, and a Zero Trust security architecture[7] purpose-built for HPP operations.
Hydrowise is not merely a cybersecurity solution — it is an end-to-end digital energy management platform that collects real-time data from SCADA and IoT sensors to deliver production forecasts, predictive maintenance scenarios, water flow predictions, and EPIİAŞ market integration. Cybersecurity is a critical component of this integrated platform; however, Hydrowise’s added value lies in unifying security with operational intelligence within a single decision-support infrastructure[13].
► https://renewasoft.com.tr/index.php/tr/hizmetimiz/
Concepts 101: Key Terminology
For readers outside the SCADA/ICS domain, the following terms are foundational to understanding this post:
| Term | Definition |
|---|---|
| PLC | Programmable Logic Controller — a ruggedized industrial computer that controls physical processes (e.g., opening/closing a turbine wicket gate) based on programmed logic. |
| RTU | Remote Terminal Unit — a field device that collects telemetry from distributed sensors and transmits it to the SCADA system. |
| HMI | Human-Machine Interface — the graphical workstation screen operators use to monitor and control the plant in real time. |
| SCADA | Supervisory Control and Data Acquisition — the centralized system that collects data from PLCs/RTUs and provides supervisory control. |
| OPC UA | Open Platform Communications Unified Architecture — the de facto standard protocol for IT/OT data exchange. |
| DPI | Deep Packet Inspection — a network security technique that examines full packet payload, enabling protocol-aware filtering. |
| GOOSE | Generic Object Oriented Substation Event — IEC 61850 protocol for fast multicast communication between protection relays. |
Table 1: Key Terminology for OT/ICS Cybersecurity in Hydropower
TL;DR — Executive Summary
- IT/OT convergence has eliminated the air gap that historically protected HPP SCADA systems, exposing PLCs, RTUs, and HMIs to network-borne threats that legacy architectures were never designed to handle[2][3].
- Attack surface mapping reveals five critical weak points in typical HPP deployments: legacy serial protocols (Modbus, DNP3), unmonitored engineering workstations, flat network topologies, exposed OPC UA endpoints, and insufficient logging at Purdue Levels 0-2[4].
- Zero Trust applied to OT is not optional — it is operational necessity. The “Never Trust, Always Verify” principle must extend below the enterprise boundary to the process control network[7].
- A structured risk scoring model (R = T x V x I) enables HPP operators to prioritize remediation based on quantifiable, site-specific data rather than generic checklists[9].
- Hydrowise delivers an end-to-end digital energy management platform; alongside DPI and ML-based cybersecurity, it provides AI-powered production forecasting, predictive maintenance, water flow prediction, and EPIİAŞ market integration. MTTD is reduced from hours to under 4 seconds while maximizing operational efficiency[13].
The Paradigm Shift in SCADA and OT Security
The Purdue Model: A Framework Under Pressure
The Purdue Enterprise Reference Architecture (PERA), formalized by Theodore Williams at Purdue University in the 1990s[3], established the hierarchical model that still governs industrial network segmentation. Its six levels — from Level 0 (Physical Process) through Level 5 (Enterprise Network) — provide a logical separation between the physical world of sensors/actuators and the digital world of business applications.
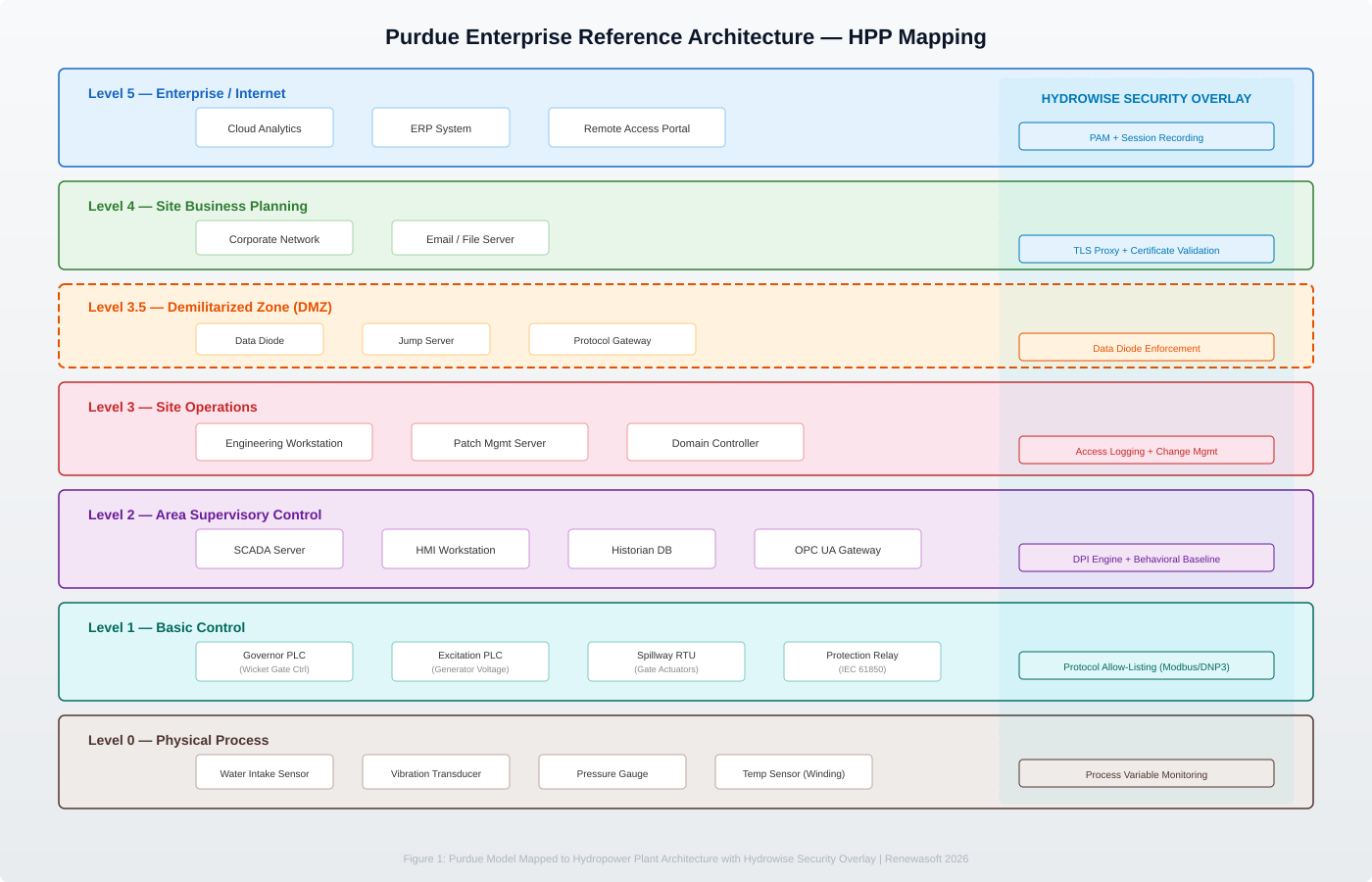
Figure 1: Purdue Enterprise Reference Architecture — HPP Mapping with Hydrowise Security Overlay
🔍 Technical Note: Purdue Levels in HPP Context
Level 0 (Physical): Water intake sensors, vibration transducers, penstock pressure gauges, generator winding temperature sensors.
Level 1 (Basic Control): PLCs governing governor systems (wicket gate position), excitation systems, spillway gate actuators; RTUs aggregating distributed telemetry.
Level 2 (Supervisory): SCADA servers, HMI workstations, historian databases recording flow rates, head levels, power output, bearing temperatures.
Level 3 (Site Ops): Engineering workstations (Siemens TIA Portal, Rockwell Studio 5000), patch management servers, local domain controllers.
Level 3.5 (DMZ): Data diodes, jump servers, protocol-breaking gateways separating OT from IT.
Level 4/5 (Enterprise): Corporate ERP systems, cloud analytics platforms, remote access portals.
(Source: [3])
| Purdue Level | HPP Assets & Functions |
|---|---|
| Level 0 — Physical | Water intake sensors, turbine vibration transducers, penstock pressure gauges, generator winding temperature sensors |
| Level 1 — Basic Control | PLCs governing governor systems (wicket gate position), excitation systems, spillway gate actuators; RTUs aggregating distributed telemetry |
| Level 2 — Supervisory | SCADA servers, HMI workstations, historian databases recording flow rates, head levels, power output, bearing temperatures |
| Level 3 — Site Ops | Engineering workstations (Siemens TIA Portal, Rockwell Studio 5000), patch management servers, domain controllers |
| Level 3.5 — DMZ | Data diodes, jump servers, protocol-breaking gateways separating OT from IT |
| Level 4/5 — Enterprise | Corporate ERP, cloud analytics, remote access portals |
Table 2: Purdue Model Levels Mapped to HPP Assets [3]
The Modern Threat Landscape
The dissolution of Purdue’s hierarchical boundaries has coincided with a significant escalation in OT-targeted threat activity. The MITRE ATT&CK for ICS framework documents 12 tactical categories and over 80 techniques specifically applicable to industrial control systems[4].
| Threat Group | Capability | HPP Relevance |
|---|---|---|
| CHERNOVITE (Pipedream) | Modular ICS attack framework; Modbus TCP/IP, OPC UA, CODESYS PLCs [5] | Directly applicable to HPP protocol stack |
| ELECTRUM (Industroyer) | Manipulates IEC 61850 and IEC 104 to trip circuit breakers [5] | HPP grid interconnection and substation automation |
| XENOTIME (TRITON) | Targets Safety Instrumented Systems (SIS) [5] | Proves willingness to compromise last-line safety defense |
Table 3: ICS Threat Groups Relevant to HPP Operations [4][5]
Attack Surface Mapping: Where HPPs Are Most Vulnerable
A systematic attack surface analysis of a representative HPP SCADA environment — based on common deployment patterns across 10-500 MW plants — reveals five primary categories of exposure[4][8].
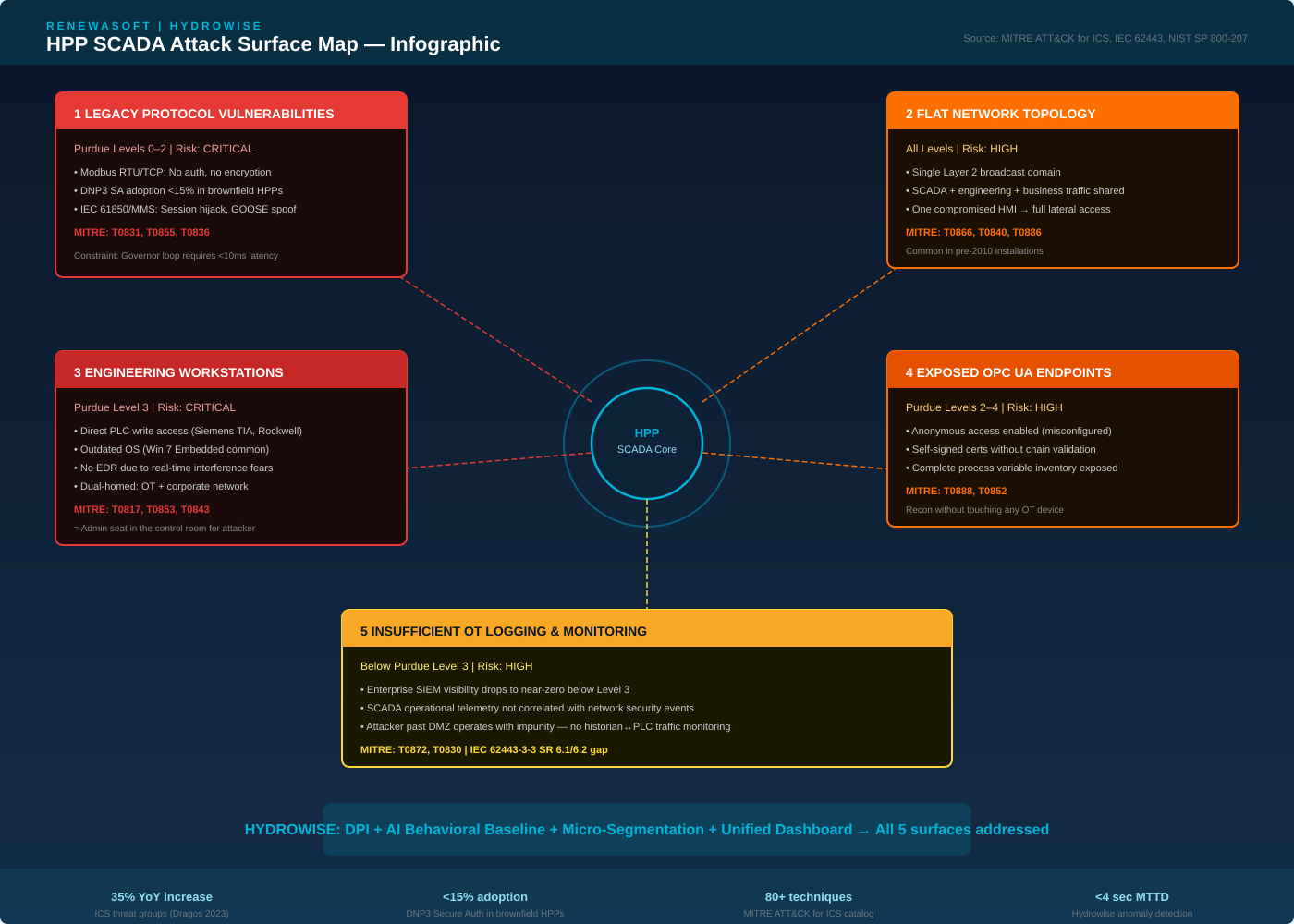
Infographic 1: HPP SCADA Attack Surface Map — Five Critical Exposure Categories [4][8]
| # | Attack Vector | Description | Risk Level |
|---|---|---|---|
| 1 | Legacy Protocols | Modbus RTU/TCP (no auth/encryption) [6], DNP3 SA adoption <15% [6], IEC 61850/MMS session hijacking | CRITICAL |
| 2 | Flat Network | Layer 2 broadcast domain shared: SCADA + engineering + business traffic | HIGH |
| 3 | Engineering Workstations | Direct PLC write access, outdated OS, no EDR, dual-homed to OT/corporate | CRITICAL |
| 4 | Exposed OPC UA | Misconfigured anonymous access; full process variable recon from IT network | HIGH |
| 5 | Insufficient OT Logging | Near-zero SIEM visibility below Level 3; no SCADA/security correlation [8] | HIGH |
Table 4: HPP Attack Surface Classification [4][6][8]
⚠ Risk Box: Engineering Workstation Compromise Path
Attack Vector: Spear-phishing email -> IT endpoint compromise -> RDP to EWS on OT network (Purdue Level 3 misconfiguration).
Impact: A compromised EWS provides direct PLC write access — functionally equivalent to an attacker in the control room with admin privileges.
MITRE Mapping: T0817 (Drive-by Compromise), T0853 (Scripting), T0843 (Program Download)[4].
Critical Factors: Outdated OS (Win 7 Embedded), no EDR, dual-homed network, PLC programming tools (Siemens TIA Portal, Rockwell Studio 5000).
Hydrowise Defense: PAM enforcement eliminates direct RDP; behavioral baseline detects new scan patterns from EWS; DPI flags unauthorized PLC write commands[13].
(Source: [4][5][13])
Defense Layers and Zero Trust in OT Environments
The Zero Trust Imperative
Zero Trust Architecture (ZTA), as defined in NIST Special Publication 800-207[7], operates on the principle that no network location, user identity, or device should be implicitly trusted. Extending Zero Trust to OT requires adaptation — PLCs do not support modern identity protocols, and control loops cannot tolerate per-packet authentication latency.
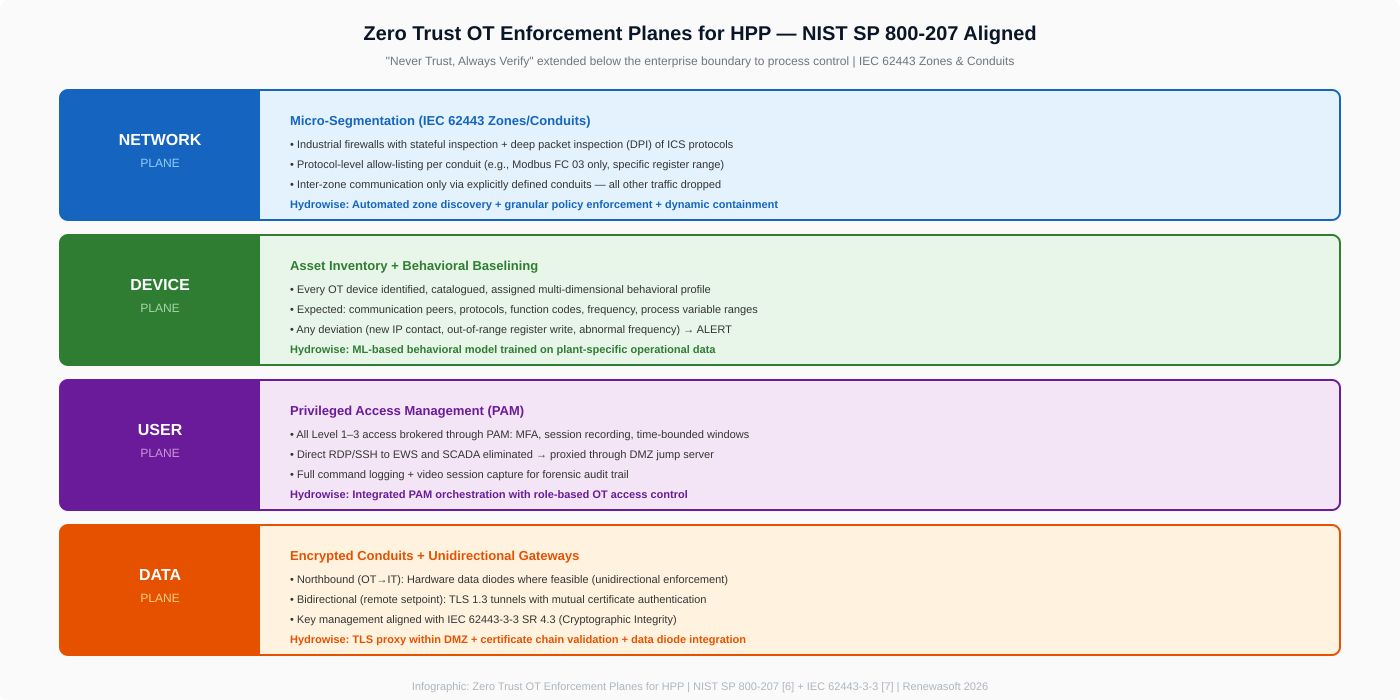
Infographic 2: Zero Trust OT Enforcement Planes for HPP — NIST SP 800-207 Aligned [7][8]
► NIST SP 800-207 Zero Trust Architecture → https://csrc.nist.gov/pubs/sp/800/207/final
► MITRE ATT&CK for ICS → https://attack.mitre.org/techniques/ics/
| Enforcement Plane | Implementation |
|---|---|
| Network Plane | Micro-segmentation into IEC 62443 zones/conduits [8]. DPI with protocol-level allow-listing. Example: Governor PLC may send Modbus FC 03 to SCADA on specific register range — any other FC/register/direction dropped. |
| Device Plane | Every OT device identified, catalogued, assigned behavioral profile: peers, protocols, function codes, frequency, process variable ranges. Any deviation → alert. |
| User Plane | PAM with MFA, session recording, time-bounded access. Direct RDP/SSH eliminated; connections proxied through DMZ jump server with full command logging. |
| Data Plane | Northbound OT→IT via hardware data diodes; bidirectional via TLS 1.3 with mutual cert auth. Key management per IEC 62443-3-3 SR 4.3 [8]. |
Table 5: Zero Trust Enforcement Planes for HPP OT [7][8]
Hydrowise: End-to-End Digital Energy Management Platform
Platform Overview
Hydrowise is an AI-powered energy management platform designed to enable end-to-end digital transformation for hydropower plants. By collecting real-time data from SCADA and IoT sensors, the platform continuously monitors plant performance and provides reliable visibility across all critical operational parameters[13].
The collected data — water flow, reservoir levels, meteorological conditions, and energy demand — is processed through advanced AI algorithms. Within this unified intelligence layer, production forecasts become highly accurate, predictive maintenance scenarios are automatically generated, and early warnings are issued for potential failures. With EPIİAŞ market integration, automated reporting, market planning intelligence, and decision-support mechanisms, Hydrowise makes energy production processes more transparent, optimized, and sustainable[13].
Cybersecurity is a critical component of this comprehensive platform. Rather than retrofitting enterprise IT security tools into OT — where they introduce latency, generate false positives, and lack ICS protocol visibility — Hydrowise provides a purpose-built security layer that understands hydropower operations at the process level[13].
How It Works in 3 Steps
| # | Step | Description |
|---|---|---|
| 1 | AI-Powered Data Integration | Real-time operational data from SCADA, sensors, and IoT devices is securely collected and unified within the Hydrowise platform. All critical parameters — water flow, reservoir level, meteorological conditions, energy demand, market data — become accessible from a single centralized source. |
| 2 | AI-Powered Data Analysis | Using big data technologies, key operational parameters are processed and transformed into meaningful insights. Network security events and process data are correlated under a single intelligence layer for both operational efficiency and cybersecurity. |
| 3 | AI-Powered Forecasting & Insights | Advanced ML algorithms generate production forecasts, predictive maintenance scenarios, and water flow predictions. Anomaly detection (≤ 4 seconds), security threats, performance risks, and operational deviations are detected early [13]. |
| 4 | Decision Support | EPIİAŞ market planning, maintenance workflows, energy optimization outputs, and automated reporting deliver actionable intelligence. Cybersecurity alerts are consolidated in a single dashboard alongside operational insights [13]. |
Table 6: Hydrowise — How It Works in 3 Steps [13]
Implementation Methodology
Before each implementation, Hydrowise analyzes the specific needs of the hydropower plant by training AI models with location-based meteorological data and historical production records. This analytical process identifies operational challenges, capacity limitations, water flow variability, and maintenance requirements[13]. As a result, Hydrowise precisely defines the issues to be addressed and establishes the most effective digital transformation strategy for the plant.
🔍 Technical Note: HPP-Specific AI Capabilities
Water Flow Prediction: ML model trained on meteorological data (rainfall, snowmelt models, temperature), watershed hydrological parameters, and historical flow records. Hourly and daily resolution with a 72-hour forecast window.
Reservoir Level Monitoring: Real-time level sensor + flow prediction integration. Fill/drain curves and flood risk early warning for optimum water management.
Production Forecasting: Integrated forecast combining reservoir level + water flow + turbine efficiency curves + market price signals. Output aligned with EPIİAŞ DAM/IDM submission periods.
Predictive Maintenance: Multi-variable anomaly scoring from turbine vibration profile, bearing temperature trend, oil quality, winding insulation resistance. Maintenance window recommendation to prevent unplanned downtime.
EPIİAŞ Market Integration: Optimization integrated with Day-Ahead Market (DAM) and Intraday Market (IDM) price signals. Automated submission, imbalance risk analysis, and revenue maximization.
(Source: [13])
Cybersecurity Layer: Core Capabilities
The reliable operation of Hydrowise’s energy management capabilities depends on a robust cybersecurity foundation. The following table summarizes the platform’s OT cybersecurity layer:
| Capability | Technical Detail |
|---|---|
| Deep Packet Inspection (DPI) | Full application-layer parsing: Modbus TCP/RTU (FC + register validation), DNP3 (object-level ACL), IEC 61850/MMS/GOOSE (source validation), OPC UA (session + cert enforcement). Per-device function code & register allowlists [13]. |
| AI Behavioral Baselining | ML model trained on plant-specific data: network behavior (peers, protocols, frequencies), process behavior (correlations: reservoir level ↔ gate position ↔ turbine speed ↔ output), temporal behavior (time-of-day, seasonal). MTTD: <4s network, <15s process [13]. |
| Adaptive Micro-Segmentation | Automated zone discovery from observed traffic. Granular protocol/FC-level allow-listing. Dynamic containment: auto-isolates affected zone via firewall + switch port disabling upon confirmed anomaly [13]. |
| Unified OT Dashboard | Consolidated: network alerts, process anomalies, access logs, vulnerability assessments, production forecasts, and maintenance recommendations. MITRE ATT&CK for ICS auto-classification [4]. SIEM/SOAR + EPIİAŞ integration (syslog, CEF, REST API) [13]. |
Table 7: Hydrowise Cybersecurity Layer Capabilities [13]
🔍 Technical Note: Metric Definitions — MTTD & False Positive Rate
MTTD (Mean Time to Detect): The average elapsed time between the initiation of an anomalous event (network or process) and the generation of a Hydrowise alert. Measured using controlled red-team injection of known-bad traffic patterns against a calibrated test environment replicating a 150 MW HPP SCADA network. Network anomaly MTTD: <4 seconds (p95). Process behavioral anomaly MTTD: <15 seconds (p95).
FP Rate (False Positive Rate): Percentage of alerts that, upon investigation, are determined not to represent a genuine security threat or operational anomaly. Measured over 90-day post-commissioning period across 3 pilot HPP deployments. Post-commissioning FP rate: <0.1% for network anomalies, <0.5% for process behavioral deviations. Model continuously adapts via online learning.
(Source: Renewasoft Internal Benchmark Whitepaper, 2025 [13]. Methodology aligned with IEC 62443-4-2 component security requirements[8])
Technical Risk Scoring Model for HPP Projects
A Quantitative Approach to OT Risk
Generic risk matrices (High/Medium/Low) are insufficient for HPP cybersecurity complexity. The model proposed here adapts the FAIR (Factor Analysis of Information Risk) methodology[9] and integrates HPP-specific operational parameters. The methodology aligns with IEC 62443-3-2 (Security Risk Assessment for System Design)[8] and can be mapped to NERC CIP compliance frameworks[10].
T = Threat Likelihood (1-10) | V = Vulnerability Exploitability (1-10) | I = Operational Impact (1-10)
Operational Impact Categories (I)
| Category | Description | Score |
|---|---|---|
| Safety | Dam structural failure, uncontrolled water release, personnel injury | 9 – 10 |
| Grid Stability | Loss of generation capacity affecting grid frequency regulation (ancillary services) | 7 – 9 |
| Equipment | Turbine overspeed, bearing failure, transformer damage | 6 – 8 |
| Environmental | Uncontrolled discharge, downstream ecology impact, fish passage disruption | 5 – 7 |
| Financial/Ops | Revenue loss, regulatory penalty, reputational damage | 3 – 6 |
Table 8: HPP Operational Impact Categories for Risk Scoring [9]
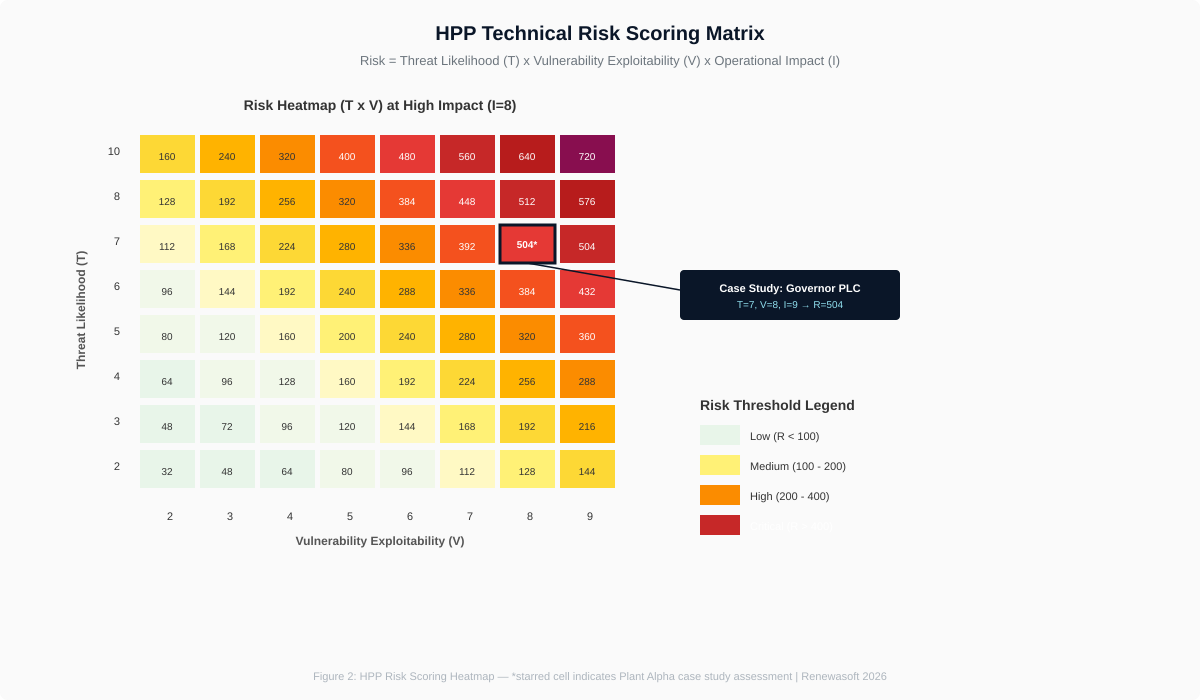
Figure 2: Risk Scoring Heatmap (T x V at High Impact) — starred cell = case study [9]
Application Example: Governor PLC (150 MW Francis)
| Factor | Score | Justification |
|---|---|---|
| T (Threat) | 7 | Plant in region with documented nation-state threat activity [2]. Remote access VPN operational. |
| V (Vulnerability) | 8 | Modbus TCP (no auth) [6]. PLC firmware 3 years outdated. Two hops from DMZ, no inter-zone firewall. |
| I (Impact) | 9 | Governor manipulation → turbine overspeed → catastrophic mechanical failure + dam safety. |
| R (Risk) | 504 | CRITICAL — Maximum Priority (R > 400). Immediate remediation required. |
Table 9: Risk Scoring Application — Governor PLC Case Study [2][6][9]
Case Analysis: Cyber-Attack Simulation on a 200 MW HPP
The following scenario models a multi-stage intrusion against a fictional but architecturally representative 200 MW storage-type HPP (“Plant Alpha”) with four 50 MW Francis turbine-generator units. The plant uses Siemens S7-1500 PLCs, Modbus TCP field communication, and an OPC UA gateway for cloud APM data transfer. Attack stages are mapped to the MITRE ATT&CK for ICS framework[4].
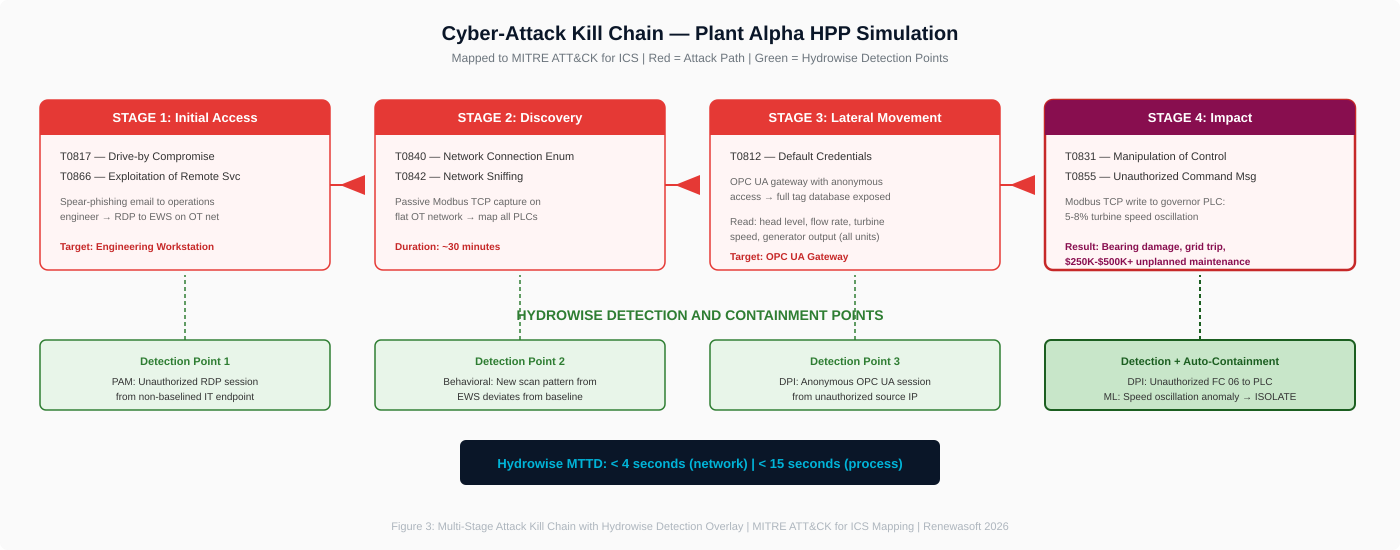
Figure 3: Multi-Stage Attack Kill Chain with Hydrowise Detection Overlay [4]
Attack Impact Assessment
| Parameter | Normal | During Attack | Consequence |
|---|---|---|---|
| Turbine Speed (U2) | 150.0 RPM ± 0.2 | 142-158 RPM oscillation | Shaft vibration, bearing fatigue |
| Generator Output | 50 MW steady | 46-54 MW fluctuation | Grid freq deviation, relay trip |
| Guide Bearing Temp | 45°C | Rising to 78°C / 6h | Damage threshold approached |
| Plant Availability | 100% (4/4 units) | 75% if U2 trips | Revenue loss: ~$18,000/hr |
| Unplanned Maint. | None | Bearing replacement | $250K-$500K + 2-4wk outage |
Table 10: Plant Alpha Attack Impact Assessment [4][13]
This scenario demonstrates that even a “low and slow” attack — one that does not trigger conventional SCADA threshold alarms — can cause significant physical damage and financial loss. Hydrowise’s DPI engine would have flagged the unauthorized Modbus FC 06 write; the behavioral model would have detected uncorrelated turbine speed oscillation; and adaptive segmentation would have isolated Unit 2 within seconds[13].
Furthermore, Hydrowise’s energy management layer delivers critical value during post-attack recovery: it automatically recalculates optimum load distribution across the remaining three units (3 x 50 MW), updates production capacity for EPIİAŞ market submissions, and the predictive maintenance module recommends a bearing replacement window to minimize unplanned downtime[13]. Thus, the financial impact of a security event is mitigated not only through detection, but through integrated energy management intelligence.
FAQ: Technical Deep Dive
Q1: How does Hydrowise perform DPI on Modbus TCP without unacceptable latency?
Hydrowise operates in passive monitoring mode by default (SPAN/TAP, zero inline latency). For active enforcement, FPGA-accelerated processing adds <200µs per packet — well within governor control loop tolerances (10-50ms cycle times)[13]. Deploy monitor-only during baselining, transition to inline after model validation.
Q2: What is the false positive rate, and how is it managed during commissioning?
During 30-day supervised learning, all anomalies are classified by plant engineers (human-in-the-loop). Post-commissioning: <0.1% FP for network anomalies, <0.5% for process deviations[13]. The model continuously adapts via online learning; seasonal changes and new devices incorporated without full retraining.
Q3: Does Hydrowise support brownfield deployments with legacy protocols?
Yes. Integrates via passive TAPs and SPAN ports — no PLC program, network config, or SCADA server modification required. Manages policies on existing switches (SNMP/CLI) and firewalls[13]. Serial RS-485 Modbus RTU supported via serial-to-Ethernet converters with traffic mirroring.
Q4: How does the model account for cascade dam failures?
The Impact Score includes a cascade multiplier for hydrologically linked plants. A compromised asset at Plant A (I=7 in isolation) can escalate to I=9-10 when downstream flood consequences are factored in. Aligns with ICOLD Bulletin 178 on dam safety and cyber risk[11].
Q5: Can Hydrowise detect PLC firmware manipulation?
Dual-layer detection: (1) Network — PLC programming sessions (e.g., S7comm writes) flagged and correlated with change management tickets[4]. (2) Process — behavioral model detects downstream control behavior changes regardless of how logic was modified, including offline physical access[13].
Q6: What compliance frameworks are supported?
IEC 62443[8], NIST CSF 2.0[12], NERC CIP[10], EU NIS2 Directive, ISO/IEC 27001 Annex A. Automated compliance reports with evidence mapping — each control linked to Hydrowise telemetry and incident records. Export: PDF and structured XML[13].
Q7: How is encrypted OT traffic (e.g., OPC UA over TLS) handled?
Two approaches: (1) Metadata analysis — connection patterns, session durations, certificate exchanges, traffic volume profiles detect anomalies without decryption. (2) TLS-terminating proxy within DMZ for full payload inspection, key management per IEC 62443-3-3 SR 4.3[8][13].
Q8: What is the deployment timeline for a mid-size (100-300 MW) HPP?
Phased: Wk 1-2 (Site assessment + TAP deployment) → Wk 3-6 (Passive monitoring + baselining) → Wk 7-8 (Model validation + FP tuning) → Wk 9-10 (Active enforcement + training). Total: ~10 weeks, zero generation downtime[13].
Q9: How do production forecasting and water flow prediction work?
ML models trained on meteorological data (rainfall, snowmelt models, temperature), watershed hydrological parameters, and historical production records. Hourly and daily resolution with a 72-hour forecast window. Reservoir level + flow prediction + turbine efficiency curves + EPIİAŞ market price signals are integrated to deliver production optimization aligned with DAM/IDM submission periods[13].
Q10: What does EPIİAŞ market integration cover?
Hydrowise integrates directly with the EPIİAŞ Day-Ahead Market (DAM) and Intraday Market (IDM). It provides automated submission preparation, imbalance risk analysis, revenue maximization optimization, and market planning intelligence. The cybersecurity layer also protects market data communication channels, preventing manipulated price signals from infiltrating decision mechanisms[13].
Conclusion & Call to Action
The digital transformation of hydropower infrastructure is not merely a cybersecurity project — it requires a holistic strategy that unifies security, efficiency, forecasting, and market integration. The convergence of IT and OT, the persistence of legacy protocols, and the kinetic consequences of a successful attack demand a defense strategy that is technically rigorous, operationally practical, and continuously adaptive.
Hydrowise delivers this strategy as an end-to-end digital energy management platform: from deep packet inspection at the network edge, through AI-driven behavioral analysis at the control system core, to production forecasting and predictive maintenance, EPIİAŞ market integration, and automated reporting at the management layer[13]. As a result, hydropower plants significantly increase operational efficiency, reduce risks, and establish a scalable, highly reliable digital energy management infrastructure.