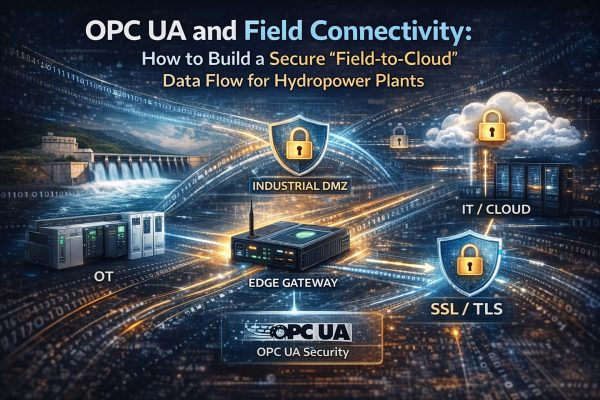
OPC UA and Field Connectivity: How to Build a Secure “Field-to-Cloud” Data Flow for Hydropower Plants
TL;DR
- OPC UA provides a security model that covers authentication, authorization, confidentiality, integrity, and auditability. [1][2]
- The safest pattern is controlled egress via an edge gateway and an industrial DMZ rather than exposing OT assets to the Internet. [3][4]
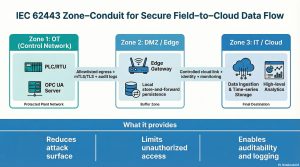
- IEC 62443 zone–conduit thinking standardizes boundaries and controlled communication paths between OT/edge/IT. [4][5]
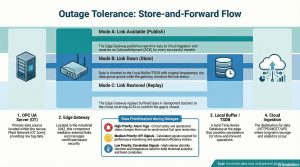
- For intermittent links, store-and-forward buffering plus local time-series persistence at the edge reduces data loss. [6][7]
- A secure and resilient architecture should integrate standardized data ingestion, time-series storage, alarm/KPI layers, and analytics within a controlled OT–IT data flow.
1) Hook: Why is “field-to-cloud” sensitive in hydropower plants?
HPP OT networks carry processes requiring high availability and low tolerance to disruption. Cloud connectivity is not just an IT task; it is a combined decision about continuity, security, and performance. NIST’s ICS guidance emphasizes that ICS components have unique requirements and that directly importing IT-only practices can be risky. [3]
2) Concepts: What does OPC UA security rely on?
OPC UA Part 2 defines security objectives such as authentication, authorization, confidentiality, integrity, auditability, and availability, and maps them to mechanisms. [1][2]
Technical Note: ‘OPC UA = enable TLS and done’ is not sufficient. You must manage application identity (certificates), user identity/roles, and node-level authorization together. [1][2]
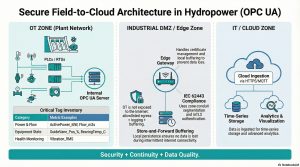
3) Reference pattern: OT → Edge/DMZ → IT/Cloud
Recommended pattern: OT Zone (PLC/RTU + OPC UA Server) → Edge/DMZ Zone (Gateway) → IT/Cloud (Ingestion + TSDB + Analytics). Principle: keep the OPC UA Server inside OT; do not expose it directly to the cloud. The edge gateway handles the external link and mediation.
3.1 Detailed Data Flow: From Tag to Cloud
A secure field-to-cloud pipeline should be designed as a deterministic data flow rather than a simple connection.
Step-by-step flow:
1) Data Source (OT Layer)
• PLC / RTU signals (e.g., MW, flow, vibration)
• Sampling frequency defined per signal criticality
2) OPC UA Server
• Exposes structured address space (namespace, node hierarchy)
• Applies node-level access control
3) Edge Gateway (DMZ Layer)
• OPC UA Client subscribes to selected nodes
• Data normalization (unit conversion, naming standard)
• Timestamp alignment (source vs ingestion time)
4) Buffer Layer (Critical for reliability)
• In-memory queue (short-term)
• Local TSDB (long-term fallback)
• Store-and-forward logic with retry policies
5) Secure Transport
• TLS encryption
• Outbound-only connection (no inbound exposure)
6) Cloud Ingestion Layer
• Message broker (Kafka / MQTT)
• Stream processing / validation
7) Storage & Analytics
• Time-series database (Timescale, Influx, etc.)
• KPI / alarm / analytics pipelines
This structure ensures that data flow remains controlled, observable, and resilient under real-world conditions.
 4) Security design: certificates, policy choices, and auditability
4) Security design: certificates, policy choices, and auditability
4.1 Certificate lifecycle (PKI): OPC UA uses X.509 certificates for application identity; trust is managed via trust lists. Operationalize renewal, revocation (CRL), and private-key protection. [1][2]
4.2 Reverse Connect: Can help in DMZ/firewall scenarios without opening inbound ports, but requires extra controls for verification and DoS risks. [8][9]
Risk Box: Reverse Connect is not a silver bullet; it requires additional security assessment. [8]
4.3 IEC 62443 zone–conduit: Define segmentation (zones) and controlled communication paths (conduits) with allowlists, inspection, and logging. [4][5]
Security Hardening Checklist (Field-to-Cloud)
• OPC UA certificates stored in secure keystore (HSM if possible)
• Private key access restricted
• Certificate rotation automated
• Trust list managed centrally
• No direct inbound connection to OT
• Firewall rules: strict allowlist only
• Deep packet inspection in DMZ (optional but recommended)
• Full audit logging of all connections
Security failures in OPC UA deployments are rarely protocol-related; they are almost always configuration-related.
5) Outage scenario: What happens if the Internet link goes down?
For intermittent connectivity, store-and-forward queues and local time-series persistence at the edge are critical. When connectivity returns, replay data in idempotent batches. Treat intermittency as a design requirement. [6]
Technical Note: Buffering priorities typically include alarm-driving tags, KPI-driving tags, and correlation signals (e.g., vibration + temperature).
Advanced Design: Store-and-Forward Reliability Model
A robust buffering strategy must define:
• Buffer size (based on outage tolerance)
• Priority queues (alarms > KPIs > raw data)
• Replay strategy (batch vs streaming)
• Idempotency (duplicate prevention)
Example:
• 1-hour outage → buffer must hold X records
• Replay → ordered + deduplicated
• Alarm tags → immediate priority replay
Failure to design this properly leads to:
• Data gaps
• Incorrect KPIs
• Broken anomaly detection models
6) Impact in an HPP: security, operations, maintenance
NIST stresses that availability and reliability are critical in ICS and that security controls must align with process safety. [3] Edge buffering and standardization reduce ‘data gaps’ that degrade PdM and alarm quality. [7]
OPC UA performance evaluations in IIoT contexts suggest that sampling and bandwidth planning are important under constrained edge resources. [10]
7) Mini deployment scenario: step-by-step rollout
1) Build a critical tag inventory (e.g., ActivePower_MW, Flow_m3s, GuideVane_Pos_%, BearingTemp_C, Vibration_RMS).
2) Place the OPC UA Server inside OT.
3) Deploy an edge/DMZ gateway with allowlisted egress.
4) Implement certificate/policy + trust list + renewal plan. [1][2]
5) Formalize segmentation with IEC 62443 zone–conduit. [4][5]
6) Enable store-and-forward and test replay under outages. [6]
7) Integrate the data flow into standardized pipelines: tag normalization, time-series storage, KPI/alarm generation, and analytics layers.
Risk Box: Common pitfalls include exposing OT directly, skipping certificate renewal, flat networks without DMZ, untested outage handling, and missing tag standardization. [3]
Technical Deep Dive: Tag Standardization Strategy
Unstandardized tags are one of the biggest blockers in scaling SCADA analytics.
Recommended structure:
Plant.Unit.SignalType.Parameter.Unit
Example:
HPP1.Turbine1.Power.Active.MW
HPP1.Turbine1.Vibration.RMS.mm_s
HPP1.Gate.Position.Percent
Standardization rules:
• Naming consistency across all units
• Explicit unit definitions
• Metadata enrichment (criticality, source, update rate)
• Mapping tables for legacy SCADA tags
Without standardization, downstream analytics (KPI, anomaly detection) become unreliable and costly to maintain.
8) Enterprise Approach: Building a Secure Field-to-Cloud Data Pipeline
A sustainable field-to-cloud architecture is not defined by connectivity alone, but by how data is standardized, secured, and operationalized.
This approach includes:
• OPC UA-based secure data extraction from OT systems
• Tag, unit, and timestamp standardization
• Time-series storage with retention and query optimization
• KPI and alarm generation layers
• Analytics and predictive maintenance integration
Security and resilience must be treated as foundational requirements, not optional enhancements.
FAQ
1) Can I expose OPC UA directly to the cloud? Technically possible, but DMZ/edge patterns are usually preferred for OT security. [3][4]
2) Is certificate management required? OPC UA security centers on certificate-based application identity. [1][2]
3) Will data be lost during outages? Store-and-forward + local persistence reduces loss. [6]
4) Why IEC 62443? It defines boundaries and controlled conduits for OT/IT segmentation. [4][5]
5) When is Reverse Connect useful? In DMZ/firewall scenarios, with additional controls. [8][9]
6) Is OPC UA performance sufficient? Sampling and bandwidth planning matter. [10]
Conclusion and Next Steps
Field-to-cloud connectivity in HPPs must simultaneously satisfy security, operational continuity, and data quality requirements.
OPC UA’s security model, IEC 62443-based segmentation, and edge gateway architectures with outage tolerance form the foundation of a sustainable and secure data pipeline.
References
[1] OPC Foundation. OPC UA Part 2: Security (OPC 10000-2). (Online Reference).
[2] OPC Foundation. OPC UA Security Architecture (Part 2). (Online Reference).
[3] NIST. SP 800-82 Rev.2: Guide to Industrial Control Systems (ICS) Security. (2015).
[4] ISA. ISA/IEC 62443 Series of Standards.
[5] ISA GCA. How to Define Zones and Conduits (IEC 62443).
[6] Engström, G. Tackling Offline and Intermittent Connectivity in IoT. (2023).
[7] An edge-computing based industrial gateway for Industry 4.0. (2024).
[8] OPC Foundation. Reverse Connect (OPC UA Part 2, Sec. 6.14).
[9] OPC Foundation. IT/OT Integration in Secure Industrial Environments – Reverse Connect. (2024).
[10] Performance Analysis of OPC UA for Industrial IIoT Environments. (2022).